|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2004:056-1: krb5 Vulnerability Assessment Details
|
MDKSA-2004:056-1: krb5 |
||
|
Check for the version of the krb5 package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2004:056-1 (krb5). Multiple buffer overflows exist in the krb5_aname_to_localname() library function that if exploited could lead to unauthorized root rights. In order to exploit this flaw, a possible hacker must first successfully authenticate to a vulnerable service, which must be configured to enable the explicit mapping or rules-based mapping functionality of krb5_aname_to_localname, which is not a default configuration. Mandrakesoft encourages all users to upgrade to these patched krb5 packages. Update: The original patch provided contained a bug where rule-based entries on systems without HAVE_REGCOMP would not work. These updated packages provide the second patch provided by Kerberos development team which fixes that behaviour. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2004:056-1 Network Security Threat Level: High Networks Security ID: 10448 Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

MITS Altair 8800 Computer Bamboo Reproduction Arduino Tested Working Assembled
$649.99
Bare S100 CPU Replacement for ALTAIR 8800 IMSAI 8080 JAIR Single Board Computer
$42.00
MITS ALTAIR 8800 Original Vintage Microcomputer
$6000.00
MITS ALTAIR 8800 Original Vintage Microcomputer S-100 Buy It Now $5999
$5999.00
Vintage The Age of Altair MITS Brochure with 1975 Price Guide
$225.00
MITS ALTAIR 8800 88-2SIO S-100 Reproduction Board
$35.00
S-100 backplane motherboard bare PCB 9 slot (for Altair/IMSAI)
$30.00
MITS ALTAIR 8800 Original Vintage Microcomputer with 14 boards - Buy It Now
$9500.00
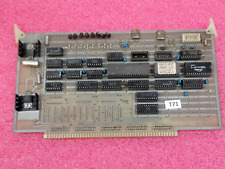
Vintage Altair 8088 CPU Wire Wrapped S100 Card w Mon EPROM circuit board #T71
$99.00
VINTAGE DEC 1975 VOL 1 ISSUE 1 SCCS INTERFACE MAGAZINE MITS ALTAIR COVER & ADS
$358.99
|
||
|
No Discussions have been posted on this vulnerability. |