|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2004:031-1: utempter Vulnerability Assessment Details
|
MDKSA-2004:031-1: utempter |
||
|
Check for the version of the utempter package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2004:031-1 (utempter). Steve Grubb discovered two potential issues in the utempter program: 1) If the path to the device contained /../ or /./ or //, the program was not exiting as it should. It would be possible to use something like /dev/../tmp/tty0, and then if /tmp/tty0 were deleted and symlinked to another important file, programs that have root rights that do no further validation can then overwrite whatever the symlink pointed to. 2) Several calls to strncpy without a manual termination of the string. This would most likely crash utempter. The updated packages are patched to correct these problems. Update: The second portion of the patch to address the manual termination of the string has been acertaind to be uneccessary, as well as reducing the length of utmp strings by one character. As such, it has been removed. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2004:031-1 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

Apple Mac Powerbook Duo 230 Vintage Laptop
$60.00
MACINTOSH QUADRA 605 RECAPPED LOGIC BOARD VINTAGE MAC APPLE COMPUTER 820-0364-A
$498.00
Apple Macintosh LC475 Model M1476 Computer Vintage For Parts or Repair
$99.95
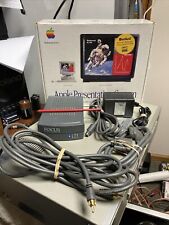
Vtg 1994 Macintosh Apple (M2895LL/A) Presentation System - All Parts/Cables Inc
$15.00
Vintage Apple Powerbook 540c Laptop Working with Original Powercord | Mac OS
$550.00
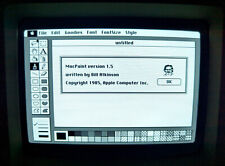
Apple Macintosh Apps - MacPaint, MacWrite, MacTerminal Floppy for Vintage Macs
$11.99
Apple Studio Display Monitor M2454 15" vintage Mac LCD
$80.00
Apple Macintosh SE/30 M5119 Vintage Mac Computer BAD FLOPPY DRIVE FOR PARTS
$350.00
Apple Macintosh LC Desktop Vintage Computer | Macintosh LC with 12" RGB Display
$199.95
Vintage Apple Macintosh Plus 1MB Desktop Computer - M0001A POWERS ON NO DRIVE
$199.95
|
||
|
No Discussions have been posted on this vulnerability. |