|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2003:115: net-snmp Vulnerability Assessment Details
|
MDKSA-2003:115: net-snmp |
||
|
Check for the version of the net-snmp package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2003:115 (net-snmp). A vulnerability in Net-SNMP versions prior to 5.0.9 could permit an existing user/community to gain access to data in MIB objects that were explicitly excluded from their view. The updated packages provide Net-SNMP version 5.0.9 which is not vulnerable to this issue and also fixes a number of other smaller bugs. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2003:115 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

Vintage Apple M7803 Pro USB Wired Keyboard Clear Black 2000
$24.99
Vintage Apple Macintosh USB Mouse M4848 Teal Round iMac Hockey Puck
$24.50
Apple Macintosh PowerBook 180 Vintage Laptop | Retro Computer
$149.95
Vintage Apple Newton eMate 300 H0208 Laptop Computer 1997 Works
$199.95
Vintage Apple Macintosh System Update Software Version 5.0 Great Condition.
$175.00
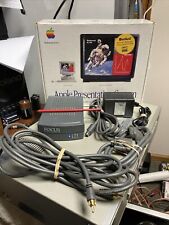
Vtg 1994 Macintosh Apple (M2895LL/A) Presentation System - All Parts/Cables Inc
$15.00
Vintage Apple M2115 External Hard Drive, Dive Not Included
$64.99
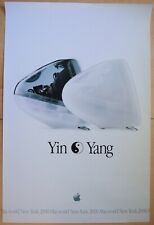
Vintage Apple iMac "Yin Yang" MacWorld New York 2002 Poster
$66.00
Vintage APPLE Color Plus 14" Display Monitor M1787 Tested
$86.00
Collection of vintage apple software and hardware manuals
$27.99
|
||
|
No Discussions have been posted on this vulnerability. |