|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2003:075-1: apache2 Vulnerability Assessment Details
|
MDKSA-2003:075-1: apache2 |
||
|
Check for the version of the apache2 package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2003:075-1 (apache2). Several vulnerabilities were discovered in Apache 2.x versions prior to 2.0.47. From the Apache 2.0.47 release notes: Certain sequences of per-directory renegotiations and the SSLCipherSuite directive being used to upgrade from a weak ciphersuite to a strong one could result in the weak ciphersuite being used in place of the new one (CVE-2003-0192). Certain errors returned by accept() on rarely accessed ports could cause temporary Denial of Service due to a bug in the prefork MPM (CVE-2003-0253). Denial of Service was caused when target host is IPv6 but FTP proxy server can't create IPv6 socket (CVE-2003-0254). The server would crash when going into an infinite loop due to too many subsequent internal redirects and nested subrequests (VU#379828). The Apache Software Foundation thanks Saheed Akhtar and Yoshioka Tsuneo for responsibly reporting these issues. To upgrade these apache packages, first stop Apache by issuing, as root: service httpd stop After the upgrade, restart Apache with: service httpd start Update: The previously released packages had a manpage conflict between apache2-common and apache-1.3 that prevented both packages from being installed at the same time. This update provides a fixed apache2-common package. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2003:075-1 Network Security Threat Level: High Networks Security ID: 8134, 8135, 8137 Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

APPLE MACINTOSH CLASSIC VINTAGE MAC Full Recap Restored Working
$225.00
Apple Mac Powerbook Duo 230 Vintage Laptop
$60.00
Apple Macintosh LC Desktop Vintage Computer | Macintosh LC with 12" RGB Display
$199.95
Vintage Apple Macintosh Plus 1MB Desktop Computer - M0001A No HDD EL4284
$49.99
Vintage Apple A1023 iSight Camera FireWire Mac Macintosh Webcam, Cord, Mount
$20.00
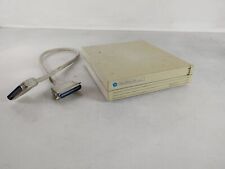
Vintage Apple DDS-0020 Macintosh DirectDrive 20 By Jasmine *NO HARD DRIVE*
$59.99
Vintage APPLE MACINTOSH SE/30 EMPTY CASE w/DISK DRIVE Compact Plus Housing
$75.00
Vintage Apple Macintosh SE Model M5011 *Powers ON
$89.99
Apple Extended Keyboard II for Mac IIgs ADB Desktop Bus Vintage M3501 M0312
$74.99
Apple Macintosh SE/30 M5119 Vintage Mac Computer BAD FLOPPY DRIVE FOR PARTS
$350.00
|
||
|
No Discussions have been posted on this vulnerability. |