|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2003:074: kernel Vulnerability Assessment Details
|
MDKSA-2003:074: kernel |
||
|
Check for the version of the kernel package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2003:074 (kernel). Multiple vulnerabilities were discovered and fixed in the Linux kernel. * CVE-2003-0001: Multiple ethernet network card drivers do not pad frames with null bytes which permits remote attackers to obtain information from previous packets or kernel memory by using special malformed packets. * CVE-2003-0244: The route cache implementation in the 2.4 kernel and the Netfilter IP conntrack module permits remote attackers to cause a Denial of Service (DoS) via CPU consumption due to packets with forged source addresses that cause a large number of hash table collisions related to the PREROUTING chain. * CVE-2003-0246: The ioperm implementation in 2.4.20 and earlier kernels does not properly restrict rights, which permits local users to gain read or write access to certain I/O ports. * CVE-2003-0247: A vulnerability in the TTY layer of the 2.4 kernel permits attackers to cause a kernel oops resulting in a DoS. * CVE-2003-0248: The mxcsr code in the 2.4 kernel permits attackers to modify CPU state registers via a malformed address. * CVE-2003-0462: A file read race existed in the execve() system call. Kernels for 9.1/x86 are also available (see MDKSA-2003:066). MandrakeSoft encourages all users to upgrade to these new kernels. For full instructions on how to properly upgrade your kernel, please review http://www.mandrakesecure.net/en/docs/magic.php. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2003:074 Network Security Threat Level: High Networks Security ID: 7791, 8042 Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

Apple Macintosh LC Desktop Vintage Computer | Macintosh LC with 12" RGB Display
$199.95
Vintage Apple M7803 Pro USB Wired Keyboard Clear Black 2000
$24.99
Vintage Apple Macintosh USB Mouse M4848 Teal Round iMac Hockey Puck
$24.50
MacEffects Gray ALPS Mechanical Keyboard for Vintage Apple IIe Computers
$195.00
Vintage Apple Keyboard II Macintosh #M0487 With Cable Ships FREE
$59.90
Vintage Apple LocalTalk Network Adapter, 6' AppleTalk cable 590-0563-A - Tested
$10.00
Vintage Apple M2115 External Hard Drive, Dive Not Included
$64.99
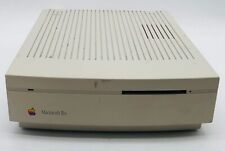
VINTAGE APPLE MACINTOSH IISi M0360 COMPUTER *AS IS*
$54.95
💻 Vintage APPLE QUANTUM PRODRIVE LPS 84S 980-80-9404 50PIN SCSI H/DRIVE Works
$99.95
Vintage Apple NUBUS Video Card 820-0600-A Macintosh Display Card
$129.00
|
||
|
No Discussions have been posted on this vulnerability. |