|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gain root remotely >> Knox Arkeia buffer overflow Vulnerability Assessment Details
|
Knox Arkeia buffer overflow |
||
|
arkeia buffer overflow Detailed Explanation for this Vulnerability Assessment It was possible to overflow a buffer in the remote Knox's Arkeia server. This problem permits a possible hacker to perform a denial of service attack and to gain root remotely on this service. Solution : upgrade to the latest version of Arkeia and/or filter incoming traffic to TCP port 617. Network Security Threat Level: High Networks Security ID: 661 Vulnerability Assessment Copyright: This script is Copyright (C) 1999 Renaud Deraison |
||
|
Cables, Connectors |

Bare S100 CPU Replacement for ALTAIR 8800 IMSAI 8080 JAIR Single Board Computer
$42.00
MITS Altair 8800 Computer Bamboo Reproduction Arduino Tested Working Assembled
$649.99
MITS ALTAIR 8800 Original Vintage Microcomputer
$6000.00
S-100 backplane motherboard bare PCB 9 slot (for Altair/IMSAI)
$30.00
Altair MITS 8800 CPU Parts Kit not IMSAI 8080 S100 (board NOT included)
$64.95
MITS ALTAIR 8800 Original Vintage Microcomputer with 14 boards - Buy It Now
$9500.00
MITS ALTAIR 8800 Original Vintage Microcomputer S-100 Buy It Now $5999
$5999.00
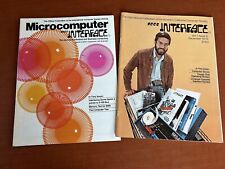
Vintage SCCS Interface Microcomputer Magazine Pair 1976 IMSAI 8080 Altair 8800
$26.00
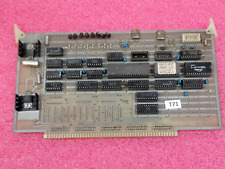
Vintage Altair 8088 CPU Wire Wrapped S100 Card w Mon EPROM circuit board #T71
$99.00
VINTAGE DEC 1975 VOL 1 ISSUE 1 SCCS INTERFACE MAGAZINE MITS ALTAIR COVER & ADS
$359.99
|
||
|
No Discussions have been posted on this vulnerability. |