|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200701-16] Adobe Acrobat Reader: Multiple vulnerabilities Vulnerability Assessment Details
|
[GLSA-200701-16] Adobe Acrobat Reader: Multiple vulnerabilities |
||
|
Adobe Acrobat Reader: Multiple vulnerabilities Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200701-16 (Adobe Acrobat Reader: Multiple vulnerabilities) Adobe Acrobat Reader in stand-alone mode is vulnerable to remote code execution via heap corruption when loading a specially crafted PDF file. The browser test released with Adobe Acrobat Reader (nppdf.so) does not properly handle URLs, and crashes if given a URL that is too long. The test does not correctly handle JavaScript, and executes JavaScript that is given as a GET variable to the URL of a PDF file. Lastly, the test does not properly handle the FDF, xml, xfdf AJAX request parameters following the # character in a URL, permiting for multiple cross-site scripting vulnerabilities. Impact A possible hacker could entice a user to open a specially crafted PDF file and execute arbitrary code with the rights of the user running Adobe Acrobat Reader. A possible hacker could also entice a user to browse to a specially crafted URL and either crash the Adobe Acrobat Reader browser test, execute arbitrary JavaScript in the context of the user's browser, or inject arbitrary HTML or JavaScript into the document being viewed by the user. Note that users who have emerged Adobe Acrobat Reader with the "nstest" USE flag disabled are not vulnerable to issues with the Adobe Acrobat Reader browser test. Workaround There is no known workaround at this time. References: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-5857 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-0044 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-0045 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-0046 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-0048 Solution: All Adobe Acrobat Reader users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=app-text/acroread-7.0.9" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2007 Michel Arboi |
||
|
Cables, Connectors |

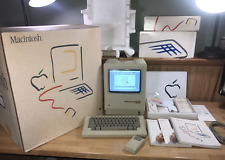
Macintosh Platinum Mouse - Apple 128K 512K 512Ke Mac Plus Lisa IIe M0100 - NEW
$44.99
Lot Of Two Vintage Apple Macintosh Computers Models 128k M0001 For Parts
$250.00
1984 APPLE MACINTOSH 128K 40th Anniversary MATCHING # BOX Set 1st Mac M0001 NICE
$7999.99
Apple Macintosh 128k 512k Plus Analog Board Capacitor Re-Cap Kit - US Shipping
$23.95
1984 Apple Macintosh 128K Mac EARLY FIRST Version RFI Foil Motherboard Shield
$29.99
Vintage Apple Macintosh Classic 128K Game Pack 3 On New 400K Double Density Disk
$39.99
1984 Apple Macintosh 128K Mac 512K RFI Foil Motherboard Shield 805-0577 REV. D
$24.99
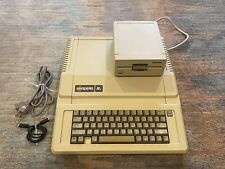
Vintage Apple lle 128k Enhanced Computer A2S2064 Rebuilt W/ Disk Drive & more
$359.99
Apple M0120 Keypad Keyboard for Macintosh 128k 512k Plus - FULLY TESTED
$99.99
Apple Macintosh 128K M0001 Computer with Mouse, no keyboard. Case included. 1984
$510.41
|
||
|
No Discussions have been posted on this vulnerability. |