|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200611-06] OpenSSH: Multiple Denial of Service vulnerabilities Vulnerability Assessment Details
|
[GLSA-200611-06] OpenSSH: Multiple Denial of Service vulnerabilities |
||
|
OpenSSH: Multiple Denial of Service vulnerabilities Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200611-06 (OpenSSH: Multiple Denial of Service vulnerabilities) Tavis Ormandy of the Google Security Team has discovered a pre-authentication vulnerability, causing sshd to spin until the login grace time has been expired. Mark Dowd found an unsafe signal handler that was vulnerable to a race condition. It has also been discovered that when GSSAPI authentication is enabled, GSSAPI will in certain cases incorrectly abort. Impact The pre-authentication and signal handler vulnerabilities can cause a Denial of Service in OpenSSH. The vulnerability in the GSSAPI authentication abort could be used to acertain the validity of usernames on some platforms. Workaround There is no known workaround at this time. References: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-5051 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-5052 http://www.openssh.com/txt/release-4.4 Solution: All OpenSSH users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=net-misc/openssh-4.4_p1-r5" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2006 Michel Arboi |
||
|
Cables, Connectors |

Vintage ATARI MEGA ST 4 4MB RAM + Keyboard + Mouse
$650.00
Vintage Atari 1040STf Computer with Mouse and Box, Minimal Testing, Pls Read
$149.99
$3200.00
Vintage Atari Megafile 44 External 44MB Drive ST STE Mega
$340.00
ATARI 4 Meg STACY ST (For Parts)
$500.00
Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
Atari 400/800/XL/XE Computer SIO2PC - PC/Mac Disk Drive Emulator Adapter/Device
$15.25
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
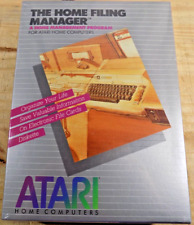
ATARI Home Computers HOME FILING MANAGER Software **SEALED NEW** 1982
$25.00
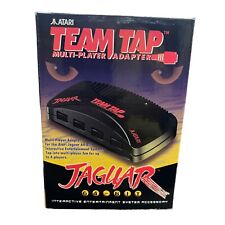
TEAM TAP Atari Jaguar Multi Player Adapter NEW In Box
$25.46
|
||
|
No Discussions have been posted on this vulnerability. |