|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200608-04] Mozilla Thunderbird: Multiple vulnerabilities Vulnerability Assessment Details
|
[GLSA-200608-04] Mozilla Thunderbird: Multiple vulnerabilities |
||
|
Mozilla Thunderbird: Multiple vulnerabilities Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200608-04 (Mozilla Thunderbird: Multiple vulnerabilities) Impact A user can be enticed to open specially crafted URLs, visit webpages containing malicious JavaScript or execute a specially crafted script. These events could lead to the execution of arbitrary code, or the installation of malware on the user's computer. Workaround There is no known workaround at this time. References: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-3113 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-3802 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-3803 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-3804 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-3805 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-3806 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-3807 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-3809 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-3810 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-3811 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-3812 Solution: All Mozilla Thunderbird users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=mail-client/mozilla-thunderbird-1.5.0.5" All Mozilla Thunderbird binary users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=mail-client/mozilla-thunderbird-bin-1.5.0.5" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2006 Michel Arboi |
||
|
Cables, Connectors |

Vintage 5362 IBM System/36 Mini-Computer Mainframe 5291 2, CRT Terminal DM12N501
$249.99
01KU751 IBM Z14 zSERIES MAINFRAME SUPPORT ELEMENT 15.5" DISPLAY UNIT
$225.00
IBM Type 4869 External 5 1/4in Floppy Disk Drive Mainframe Collection - UNTESTED
$65.00
Lot of 2 Vintage DEC Digital Computer Mainframe VT100 Keyboards Untested
$299.99
6 Vintage Computer Tape Reels mainframe 3200 5000 data ibm magnetic processor
$99.00
Vintage Silicon Graphics SGI Indy B006 Workstation Computer
$149.95
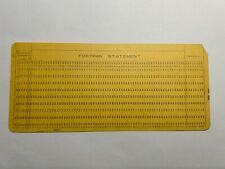
8 - VINTAGE MAINFRAME Fortran Format Punch Cards - IBM 80 columns
$9.99
VINTAGE IBM Type 4869 External 5 1/4" ~ Floppy Disk Drive Mainframe ~
$159.99
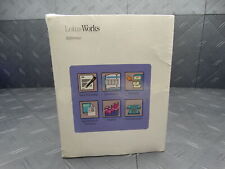
Lotus Works Vintage Software 3.5in Disks Original Seal 1990 Mainframe Collection
$431.99
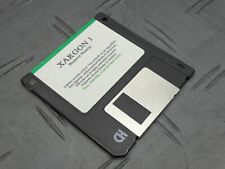
Xargon 1 Beyond Reality RARE Game Floppy 3.5” Floppy Mainframe Collection
$349.99
|
||
|
No Discussions have been posted on this vulnerability. |