|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200511-04] ClamAV: Multiple vulnerabilities Vulnerability Assessment Details
|
[GLSA-200511-04] ClamAV: Multiple vulnerabilities |
||
|
ClamAV: Multiple vulnerabilities Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200511-04 (ClamAV: Multiple vulnerabilities) ClamAV has multiple security flaws: a boundary check was performed incorrectly in petite.c, a buffer size calculation in unfsg_133 was incorrect in fsg.c, a possible infinite loop was fixed in tnef.c and a possible infinite loop in cabd_find was fixed in cabd.c . In addition to this, Marcin Owsiany reported that a corrupted DOC file causes a segmentation fault in ClamAV. Impact By sending a malicious attachment to a mail server that is hooked with ClamAV, a remote attacker could cause a Denial of Service or the execution of arbitrary code. Workaround There is no known workaround at this time. References: http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-3239 http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-3303 http://sourceforge.net/project/shownotes.php?release_id=368319 http://www.zerodayinitiative.com/advisories/ZDI-05-002.html Solution: All ClamAV users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=app-antivirus/clamav-0.87.1" Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

ASUS H110M-R Motherboard Intel 6th/7th Gen LGA1151 DDR4 Micro-ATX i/o shield
$42.00
***NEW*** BCM RX67Q Gaming Motherboard | Intel Q67 2nd/3rd Gen. | LGA1155 | DDR3
$29.77
***NEW*** BCM RX67Q mATX Gaming Motherboard Combo | Intel i5-3470 | 16GB DDR3
$49.77
Micro ATX Desktop Motherboard ASUS H110M-C LGA 1151
$31.95
ASRock B250M-HDV LGA 1151 Micro ATX DDR4 Desktop Motherboard w/ IO Shield
$54.99
Asrock Z390 Phantom Gaming 4S/AC Wifi 8th/9th Gen Intel 1151 Motherboard Bulk
$47.39
Gigabyte AMD B550 UD AC Gaming Motherboard - AMD B550 Chipset - AM4 Socket - AMD
$89.99
ASUS Prime Z390-A LGA 1151 Intel Z390 SATA USB 3.1 ATX Motherboard NO I/O
$99.00
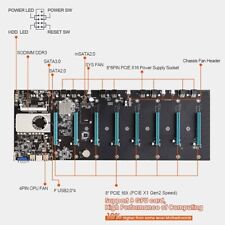
BTC-S37 Mining Motherboard Kit /w SSD & Ram Preinstalled
$59.99
GIGABYTE MB10-Datto Motherboard Xeon D-1521- SR2DF 2.40 GHz- Open Box
$115.00
|
||
|
No Discussions have been posted on this vulnerability. |