|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200502-32] UnAce: Buffer overflow and directory traversal vulnerabilities Vulnerability Assessment Details
|
[GLSA-200502-32] UnAce: Buffer overflow and directory traversal vulnerabilities |
||
|
UnAce: Buffer overflow and directory traversal vulnerabilities Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200502-32 (UnAce: Buffer overflow and directory traversal vulnerabilities) Ulf Harnhammar discovered that UnAce suffers from buffer overflows when testing, unpacking or listing specially crafted ACE archives (CVE-2005-0160). He also found out that UnAce is vulnerable to directory traversal attacks, if an archive contains "./.." sequences or absolute filenames (CVE-2005-0161). Impact A possible hacker could exploit the buffer overflows to execute malicious code or the directory traversals to overwrite arbitrary files. Workaround There is no known workaround at this time. References: http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0160 http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0161 Solution: All UnAce users should upgrade to the latest available 1.2 version: # emerge --sync # emerge --ask --oneshot --verbose ">=app-arch/unace-1.2b-r1" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

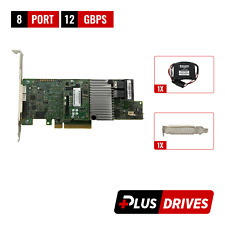
LSI 9207-8i 8-Port SAS Non-RAID 6GBPS PCIe Host Bus Adapter
$34.95
Oracle 7085209 LSI MegaRAID SAS 9361-8i 1GB Cache 12Gbps SAS/SATA PCIe RAID Card
$28.20
Cisco UCS LSI MegaRAID 9271CV-8I SAS2308 PCIe SAS Internal RAID Controller
$28.00
LSI 9223-8I 6GBPS PCIe SAS Internal RAID Controller
$22.75
Inspur LSI 9300-8i Raid Card 12Gbps HBA HDD Controller High Profile IT MODE
$15.98
LSI MegaRAID 9361-8i 12Gb PCIe 8-Port SAS/SATA RAID 1Gb w/BBU/CacheVault/License
$39.95
LSI MegaRAID 9361-8i 12Gbps PCIe 3 x8 SATA SAS 3 8 Port RAID + BBU & CacheVault
$39.00
ORICO Multi Bay RAID Hard Drive Enclosure USB 3.0/ Type-C For 2.5/3.5'' HDD SSDs
$82.49
ACASIS 2.5/3.5 inch 2 Bay SATA USB 3.0 Hard Drive Disk HDD SSD Enclosure 4 RAID
$58.99
2 Bay RAID Hard Drive Enclosure USB 3.0 Type-B for 2.5" SATA SSD/HDD Enclosure
$59.99
|
||
|
No Discussions have been posted on this vulnerability. |