|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200412-12] Adobe Acrobat Reader: Buffer overflow vulnerability Vulnerability Assessment Details
|
[GLSA-200412-12] Adobe Acrobat Reader: Buffer overflow vulnerability |
||
|
Adobe Acrobat Reader: Buffer overflow vulnerability Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200412-12 (Adobe Acrobat Reader: Buffer overflow vulnerability) A buffer overflow has been discovered in the email processing of Adobe Acrobat Reader. This flaw exists in the mailListIsPdf function, which checks if the input file is an email message containing a PDF file. Impact A remote attacker could send the victim a specially-crafted email and PDF attachment, which would trigger the buffer overflow and possibly lead to the execution of arbitrary code with the permissions of the user running Adobe Acrobat Reader. Workaround There is no known workaround at this time. References: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2004-1152 http://www.adobe.com/support/techdocs/331153.html Solution: All Adobe Acrobat Reader users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=app-text/acroread-5.10" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

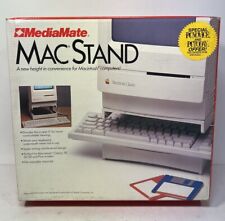
Vintage MediaMate Early 90’s Macintosh Mac Desktop PC Home Computer Stand #18200
$50.00
Vintage Keytronic PC/AT VT Switch FCC ID:CIG8AVE03435 TESTED WORKING
$30.00
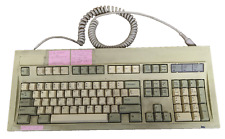
NMB KEYBOARD RT2258TW NMB PS/2 BEIGE 121944-101 REV A VINTAGE NEW OLD STOCK
$25.99
Vintage Apple MacWorld Magazine Mousepad
$15.00
Vintage Apple Support Tools Mousepad
$15.00
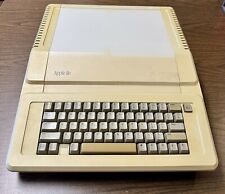
Apple IIe A2S2064 Vintage Personal Computer 128K Enhanced
$200.00
KByte ZipIt Wireless Messenger Vintage Retro Handheld Secure Messaging K Byte
$89.99
Vintage Quantum Bigfoot TS 9.6 GB AT TS09A109 REV 02-E 5.25" IDE Hard drive HDD
$32.00
NCR Mechanical Clicky Keyboard Vintage H0150-STD1-12-17 Rare (2 Missing Keys)
$179.00
VINTAGE APPLE POWER MACINTOSH 6500/250 DESKTOP COMPUTER POWERPC BOOTS
$249.50
|
||
|
No Discussions have been posted on this vulnerability. |