|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200406-15] Usermin: Multiple vulnerabilities Vulnerability Assessment Details
|
[GLSA-200406-15] Usermin: Multiple vulnerabilities |
||
|
Usermin: Multiple vulnerabilities Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200406-15 (Usermin: Multiple vulnerabilities) Usermin contains two security vulnerabilities. One fails to properly sanitize email messages that contain malicious HTML or script code and the other could permit a possible hacker to lock out a valid user by sending an invalid username and password. Impact By sending a specially crafted e-mail, a possible hacker can execute arbitrary scripts running in the context of the victim's browser. This can be lead to cookie theft and potentially to compromise of user accounts. Furthermore, a possible hacker could lock out legitimate users by sending invalid login information. Workaround There is no known workaround at this time. All users are encouraged to upgrade to the latest available version. References: http://www.securityfocus.com/bid/10521 http://www.lac.co.jp/security/csl/intelligence/SNSadvisory_e/75_e.html Solution: Usermin users should upgrade to the latest version: # emerge sync # emerge -pv ">=app-admin/usermin-1.080" # emerge ">=app-admin/usermin-1.080" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

WD_BLACK 1TB 2.5-inch Performance Hard Drive - WD10SPSX
$69.99
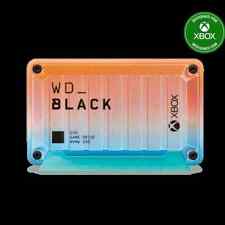
WD_BLACK 1TB D30 Game Drive SSD for Xbox Summer Collection - WDBAMF0010BSU-WESN
$109.99
SanDisk 1TB Extreme Portable SSD, External Solid State Drive - SDSSDE61-1T00-G25
$99.99
SanDisk 1TB Ultra Dual Drive Go USB Type-C Flash Drive, Black - SDDDC3-1T00-G46
$109.99
1TB Samsung 850 Pro Series 2.5" SATA 3 SSD MZ-7KE1T0BW HDD hard drive MZ-7KE1T0
$59.99
SEAGATE ST1000DM003 1TB SATA 3.5”HARD DRIVE
$11.19
Patriot P210 128GB 256GB 512GB 1TB 2TB 2.5" SATA 3 6GB/s Internal SSD PC/MAC Lot
$19.99
Samsung - Geek Squad Certified Refurbished 870 EVO 1TB SATA Solid State Drive
$67.99
1TB/2TB USB 3.0 Flash Drive Thumb U Disk Memory Stick Pen PC Laptop Storage lot
$80.39
Toshiba DT01ABA100V 3.5" SATA Internal Hard Drive 1TB Tested/Wiped
$15.00
|
||
|
No Discussions have been posted on this vulnerability. |