|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200405-19] Opera telnet URI handler file creation/truncation vulnerability Vulnerability Assessment Details
|
[GLSA-200405-19] Opera telnet URI handler file creation/truncation vulnerability |
||
|
Opera telnet URI handler file creation/truncation vulnerability Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200405-19 (Opera telnet URI handler file creation/truncation vulnerability) The telnet URI handler in Opera does not check for leading '-' characters in the host name. Consequently, a maliciously-crafted telnet:// link may be able to pass options to the telnet program itself. One example would be the following: telnet://-nMyFile If MyFile exists in the user's home directory and the user clicking on the link has write permissions to it, the contents of the file will be overwritten with the output of the telnet trace information. If MyFile does not exist, the file will be created in the user's home directory. Impact This exploit has two possible impacts. First, it may create new files in the user's home directory. Second, and far more serious, it may overwrite existing files that the user has write permissions to. A possible hacker with some knowledge of a user's home directory might be able to destroy important files stored within. Workaround Disable the telnet URI handler from within Opera. References: http://www.idefense.com/application/poi/display?id=104&type=vulnerabilities&flashstatus=true Solution: All Opera users are encouraged to upgrade to the latest version of the program: # emerge sync # emerge -pv ">=net-www/opera-7.50_beta1" # emerge ">=net-www/opera-7.50_beta1" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

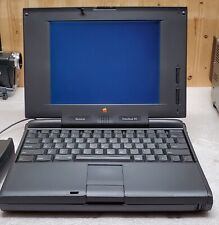
Apple Mac Powerbook Duo 230 Vintage Laptop
$60.00
Vintage Apple Macintosh SE Case - Empty Shell - Housing retro project
$60.00
Vintage Apple Macintosh II 2 M5000 Computer no power very nice w drives card
$350.00
Vintage Apple Macintosh Powerbook 190 Series M3047 Laptop Parts/Repair
$69.00
Apple Mac IIsi computer Very Good condition Vintage
$100.00
Vintage Macintosh PowerBook 140 Laptop Apple Stickers MacBook UNTESTED
$100.00
VINTAGE REFURBISHED MACINTOSH SE WITH BLUESCSI RECAPPED POWER SUPPLY
$300.00
Apple Studio Display Monitor M2454 15" vintage Mac LCD
$80.00
Apple Macintosh SE/30 M5119 Vintage Mac Computer BAD FLOPPY DRIVE FOR PARTS
$350.00
APPLE MACINTOSH PLUS M0001A Vintage Mac Computer Tested Working
$799.99
|
||
|
No Discussions have been posted on this vulnerability. |