|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200402-06] Updated kernel packages fix the AMD64 ptrace vulnerability Vulnerability Assessment Details
|
[GLSA-200402-06] Updated kernel packages fix the AMD64 ptrace vulnerability |
||
|
Updated kernel packages fix the AMD64 ptrace vulnerability Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200402-06 (Updated kernel packages fix the AMD64 ptrace vulnerability) A vulnerability has been discovered by Andi Kleen in the ptrace emulation code for AMD64 platforms when eflags are processed, permiting a local user to obtain elevated priveleges. The Common Vulnerabilities and Exposures project, http://cve.mitre.org, has assigned CVE-2004-0001 to this issue. Impact Only users of the AMD64 platform are affected: in this scenario, a user may be able to obtain elevated priveleges, including root access. However, no public exploit is known for the vulnerability at this time. Workaround There is no temporary workaround - a kernel upgrade is required. A list of unaffected kernels is provided along with this announcement. Solution: Users are encouraged to upgrade to the latest available sources for their system: # emerge sync # emerge -pv your-favourite-sources # emerge your-favourite-sources # # Follow usual procedure for compiling and installing a kernel. # # If you use genkernel, run genkernel as you would do normally. # # IF YOUR KERNEL IS MARKED as "remerge required!" THEN # # YOU SHOULD UPDATE YOUR KERNEL EVEN IF PORTAGE # # REPORTS THAT THE SAME VERSION IS INSTALLED. Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

AUDIO CODES MP-114 VOIP Gateway Open Box
$37.49
$199.99
Cisco CP-8832-K9 Unified 8800 Series Conference VOIP IP Phone 1 Year Warranty
$139.00
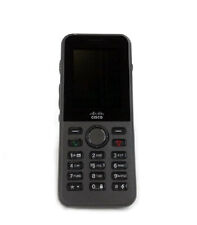
Cisco CP-8821-K9 8821 Wireless VOIP IP Phone 1 Year Waranty
$330.00
Cisco CP-7945G VOIP Phone With Stand & Handset Business IP Phone 7945
$3.00
New Cisco 7945G IP VoIP Gigabit GIGE Telephone Phone CP-7945G -
$24.95
Yealink SIP-T41P PoE Ultra Elegant VoIP Phone
$29.95
Cisco CP-8845-K9 5 Line IP Video Phone - Charcoal
$25.00
Grandstream GS-HT802 2 Port Analog Telephone Adapter VoIP Phone & Device, Black
$32.00
Cisco 8841 CP-8841-K9 VoIP Business IP Phone (Charcoal)
$49.00
|
||
|
No Discussions have been posted on this vulnerability. |