|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Remote file access >> FileMakerPro Detection Vulnerability Assessment Details
|
FileMakerPro Detection |
||
|
connects to port 49727 and says 'hello' Detailed Explanation for this Vulnerability Assessment The remote host is running a FileMakerPro server on this port. There is a flaw in the design of the FileMakerPro server which makes the database authentication occur on the client side. A possible hacker may exploit this flaw to gain access to your databases without knowing their password, only by connecting to this port with a rogue client. Solution : Do not store any sensitive data in your FileMakerPro database. Network Security Threat Level: High Networks Security ID: 7315 Vulnerability Assessment Copyright: This script is (C) 2003 Renaud Deraison |
||
|
Cables, Connectors |

Vintage Microsoft Office 2000 Premium 4 CDs + Product Keys + Service Pack CD
$59.99
Vintage Intel UPI-41 Universal Peripheral Interface User's Manual
$24.99
Vintage 1991 Hewlett Packard DeskJet 500 Printer Manual Bundle W Floppy Disk
$23.99
VINTAGE DEC DIGITAL DISK FOR RK 05 HARD DRIVE / DECPACK 2200 BPI-16
$95.00
Vintage Tandy Radio Shack Model 102 Portable Computer
$140.00
Vintage Microsoft Windows 95 Upgrade CD-ROM Edition
$12.12
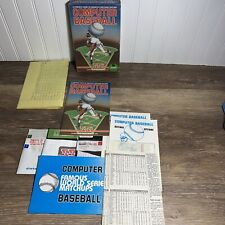
Vintage COMPUTER BASEBALL GAME- SSI- Retro- 48k Atari, Commodore 64 Floppy Disk
$35.00
Vintage CARDCO Vic-20 C64 +4 C16 and C128 Parallel Printer Interface Card - QTY
$19.99
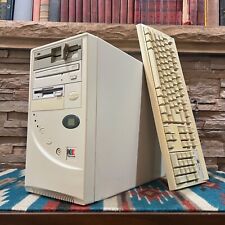
Vintage Retro AT PC Tower - Pentium MMX 166 24MB 3.5 5.25" Sound Keyboard POSTS
$199.00
Vintage 1986 IBM 1389262 Model M buckling spring terminal keyboard -1 keycap
$150.00
|
||
|
No Discussions have been posted on this vulnerability. |