|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Fedora Local Security Checks >> Fedora Core 2 2004-289: gtk2 Vulnerability Assessment Details
|
Fedora Core 2 2004-289: gtk2 |
||
|
Check for the version of the gtk2 package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory FEDORA-2004-289 (gtk2). GTK+ is a multi-platform toolkit for creating graphical user interfaces. Offering a complete set of widgets, GTK+ is suitable for projects ranging from small one-off tools to complete application suites. Update Information: During testing of a previously fixed flaw in Qt (CVE-2004-0691), a flaw was discovered in the BMP image processor of gtk2. A possible hacker could create a carefully crafted BMP file which would cause an application to enter an infinite loop and not respond to user input when the file was opened by a victim. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2004-0753 to this issue. During a security audit Chris Evans discovered a stack and a heap overflow in the XPM image decoder. A possible hacker could create a carefully crafted XPM file which could cause an application linked with gtk2 to crash or possibly execute arbitrary code when the file was opened by a victim. (CVE-2004-0782, CVE-2004-0783) Chris Evans also discovered an integer overflow in the ICO image decoder. A possible hacker could create a carefully crafted ICO file which could cause an application linked with gtk2 to crash when the file was opened by a victim. (CVE-2004-0788) Solution : http://www.fedoranews.org/updates/FEDORA-2004-289.shtml Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

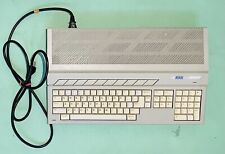
Vintage Atari 1040STf Computer with Mouse and Box, Minimal Testing, Pls Read
$149.99
Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
Atari 400/800/XL/XE Computer SIO2PC - PC/Mac Disk Drive Emulator Adapter/Device
$15.25
Atari Mega STE or TT Keyboard. Used. Untested.
$300.00
Paper Clip Word Processor Floppy Disk -Commodore 64 / Atari 800XL / 65XE / 130XE
$19.99
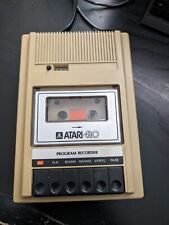
Atari 410 Program Cassette Recorder Clean Tested for power/4 cassettes/Cover
$22.99
Rare Vintage Collectible Original Atari 800 Home Computer With Case - UNTESTED
$219.99
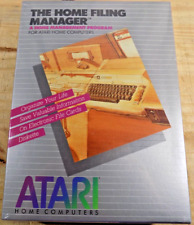
ATARI Home Computers HOME FILING MANAGER Software **SEALED NEW** 1982
$25.00
Rare Vintage Atari XF551 Floppy Disk Drive Station for 400, 800, 600, XE and XL
$300.00
|
||
|
No Discussions have been posted on this vulnerability. |