|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA868] DSA-868-1 mozilla-thunderbird Vulnerability Assessment Details
|
[DSA868] DSA-868-1 mozilla-thunderbird |
||
|
DSA-868-1 mozilla-thunderbird Detailed Explanation for this Vulnerability Assessment Several security-related problems have been discovered in Mozilla and derived programs. Some of the following problems don't exactly apply to Mozilla Thunderbird, even though the code is present. In order to keep the codebase in sync with upstream it has been altered nevertheless. The Common Vulnerabilities and Exposures project identifies the following problems: Tom Ferris discovered a bug in the IDN hostname handling of Mozilla that permits remote attackers to cause a denial of service and possibly execute arbitrary code via a hostname with dashes. A buffer overflow permits remote attackers to execute arbitrary code via an XBM image file that ends in a large number of spaces instead of the expected end tag. Mats Palmgren discovered a buffer overflow in the Unicode string parser that permits a specially crafted Unicode sequence to overflow a buffer and cause arbitrary code to be executed. Remote attackers could spoof HTTP headers of XML HTTP requests via XMLHttpRequest and possibly use the client to exploit vulnerabilities in servers or proxies. Remote attackers could spoof DOM objects via an XBL control that implements an internal XPCOM interface. Georgi Guninski discovered an integer overflow in the JavaScript engine that might permit remote attackers to execute arbitrary code. Remote attackers could execute Javascript code with chrome rights via an about: page such as about:mozilla. Remote attackers could spawn windows without user interface components such as the address and status bar that could be used to conduct spoofing or phishing attacks. Peter Zelezny discovered that shell metacharacters are not properly escaped when they are passed to a shell script and permit the execution of arbitrary commands, e.g. when a malicious URL is automatically copied from another program into Mozilla as default browser. For the stable distribution (sarge) these problems have been fixed in version 1.0.2-2.sarge1.0.7. For the unstable distribution (sid) these problems have been fixed in version 1.0.7-1. We recommend that you upgrade your mozilla-thunderbird package. Solution : http://www.debian.org/security/2005/dsa-868 Network Security Threat Level: High Networks Security ID: 14784 Vulnerability Assessment Copyright: This script is (C) 2007 Michel Arboi |
||
|
Cables, Connectors |

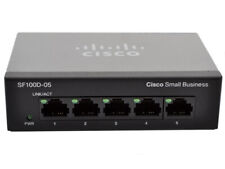
Cisco (SG100D-05-UK) 5-Ports External Ethernet Switch
$40.00
Cisco SG110 24 Port Gigabit Ethernet Switch w/ 2 x SFP SG110-24
$117.00
HP Procurve 2824 24 Gigabit Ports 10/100/1000 External Managed Switch J4903A
$74.99
Cisco SG95-16 16-Port Gigabit Switch SG95-16-SG
$47.00
Juniper Networks EX3300-48P 48-Port PoE+ 4x SFP+ Network Switch w/ Power Cord
$43.95
New Linksys SE3005 5-port Gigabit Ethernet Switch
$18.99
Linksys SE3008 8 Ports Rack Mountable Gigabit Ethernet Switch
$21.99
New 10/100 Mbps 8 Ports Fast Ethernet LAN Desktop RJ45 Network Switch Hub
$11.49
Netgear Prosafe Plus JGS524PE 24 Port Gigabit Switch 12 Port PoE JGS524PE-100NAS
$129.98
Fortinet FortiSwitch FS-124D-POE 24 Port Gigabit Ethernet Switch UNREGISTERED
$99.97
|
||
|
No Discussions have been posted on this vulnerability. |