|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA851] DSA-851-1 openvpn Vulnerability Assessment Details
|
[DSA851] DSA-851-1 openvpn |
||
|
DSA-851-1 openvpn Detailed Explanation for this Vulnerability Assessment Several security related problems have been discovered in openvpn, a Virtual Private Network daemon. The Common Vulnerabilities and Exposures project identifies the following problems: Wrong processing of failed certificate authentication when running with "verb 0" and without TLS authentication can lead to a denial of service by disconnecting the wrong client. Wrong handling of packets that can't be decrypted on the server can lead to the disconnection of unrelated clients. When running in "dev tap" Ethernet bridging mode, openvpn can exhaust its memory by receiving a large number of spoofed MAC addresses and hence denying service. Simultaneous TCP connections from multiple clients with the same client certificate can cause a denial of service when --duplicate-cn is not enabled. The old stable distribution (woody) does not contain openvpn packages. For the stable distribution (sarge) these problems have been fixed in version 2.0-1sarge1. For the unstable distribution (sid) these problems have been fixed in version 2.0.2-1. We recommend that you upgrade your openvpn package. Solution : http://www.debian.org/security/2005/dsa-851 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is (C) 2007 Michel Arboi |
||
|
Cables, Connectors |

ASUS H110M-R Motherboard Intel 6th/7th Gen LGA1151 DDR4 Micro-ATX i/o shield
$42.00
***NEW*** BCM RX67Q Gaming Motherboard | Intel Q67 2nd/3rd Gen. | LGA1155 | DDR3
$29.77
***NEW*** BCM RX67Q mATX Gaming Motherboard Combo | Intel i5-3470 | 16GB DDR3
$49.77
Micro ATX Desktop Motherboard ASUS H110M-C LGA 1151
$31.95
Gigabyte AMD B550 UD AC Gaming Motherboard - AMD B550 Chipset - AM4 Socket - AMD
$89.99
ASUS Prime Q270M-C LGA1151 DP HDMI VGA SATA 6GB/s USB 3.0 MicroATX Motherboard
$37.99
Gigabyte GA-B75M-HD3 Intel LGA1155 DDR3 Desktop Motherboard MicroATX USB 3.0
$26.99
MSI B450M PRO-VDH MAX AM4 AMD B450 USB3.2 Micro-ATX Motherboard
$67.99
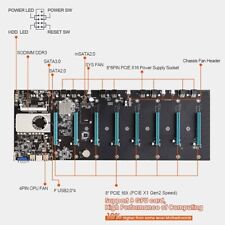
BTC-S37 Mining Motherboard Kit /w SSD & Ram Preinstalled
$59.99
GIGABYTE Z690 AORUS Elite AX (LGA 1700/Intel 7690/WiFi 6) - Gaming Motherboard
$99.86
|
||
|
No Discussions have been posted on this vulnerability. |