|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA702] DSA-702-1 imagemagick Vulnerability Assessment Details
|
[DSA702] DSA-702-1 imagemagick |
||
|
DSA-702-1 imagemagick Detailed Explanation for this Vulnerability Assessment Several vulnerabilities have been discovered in ImageMagick, a commonly used image manipulation library. These problems can be exploited by a carefully crafted graphic image. The Common Vulnerabilities and Exposures project identifies the following problems: Tavis Ormandy discovered a format string vulnerability in the filename handling code which permits a remote attacker to cause a denial of service and possibly execute arbitrary code. Andrei Nigmatulin discovered a denial of service condition which can be caused by an invalid tag in a TIFF image. Andrei Nigmatulin discovered that the TIFF decoder is vulnerable to accessing memory out of bounds which will result in a segmentation fault. Andrei Nigmatulin discovered a buffer overflow in the SGI parser which permits a remote attacker to execute arbitrary code via a specially crafted SGI image file. For the stable distribution (woody) these problems have been fixed in version 5.4.4.5-1woody6. For the unstable distribution (sid) these problems have been fixed in version 6.0.6.2-2.2. We recommend that you upgrade your imagemagick package. Solution : http://www.debian.org/security/2005/dsa-702 Network Security Threat Level: High Networks Security ID: 12875 Vulnerability Assessment Copyright: This script is (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

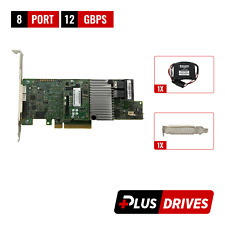
LSI 9207-8i 8-Port SAS Non-RAID 6GBPS PCIe Host Bus Adapter
$34.95
Oracle 7085209 LSI MegaRAID SAS 9361-8i 1GB Cache 12Gbps SAS/SATA PCIe RAID Card
$28.20
Cisco UCS LSI MegaRAID 9271CV-8I SAS2308 PCIe SAS Internal RAID Controller
$28.00
LSI 9223-8I 6GBPS PCIe SAS Internal RAID Controller
$22.75
Inspur LSI 9300-8i Raid Card 12Gbps HBA HDD Controller High Profile IT MODE
$15.98
LSI MegaRAID 9361-8i 12Gb PCIe 8-Port SAS/SATA RAID 1Gb w/BBU/CacheVault/License
$39.95
LSI MegaRAID 9361-8i 12Gbps PCIe 3 x8 SATA SAS 3 8 Port RAID + BBU & CacheVault
$39.00
ORICO Multi Bay RAID Hard Drive Enclosure USB 3.0/ Type-C For 2.5/3.5'' HDD SSDs
$82.49
HDD Enclosure USB 3.0 2.5 inch Dual Bay 2*6TB HDD RAID SATA Hard Drive Enclosure
$32.69
Dell LSI 9440-8i MegaRAID 8 Port 12GB/s HBA High Profile RAID Controller YW3J6
$84.99
|
||
|
No Discussions have been posted on this vulnerability. |