|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA678] DSA-678-1 netkit-rwho Vulnerability Assessment Details
|
[DSA678] DSA-678-1 netkit-rwho |
||
|
DSA-678-1 netkit-rwho Detailed Explanation for this Vulnerability Assessment "Vlad902" discovered a vulnerability in the rwhod program that can be used to crash the listening process. The broadcasting one is unaffected. This vulnerability only affects little endian architectures (i.e. on Debian: alpha, arm, ia64, i386, mipsel, and s390). For the stable distribution (woody) this problem has been fixed in version 0.17-4woody2. For the unstable distribution (sid) this problem has been fixed in version 0.17-8. We recommend that you upgrade your rwhod package. Solution : http://www.debian.org/security/2005/dsa-678 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

MITS Altair 680 Case Only LAST ONE LS3
$500.00
Bare S100 CPU Replacement for ALTAIR 8800 IMSAI 8080 JAIR Single Board Computer
$42.00
MITS Altair 8800 Computer Bamboo Reproduction Arduino Tested Working Assembled
$649.99
MITS ALTAIR 8800 Original Vintage Microcomputer
$6000.00
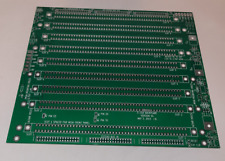
S-100 backplane motherboard bare PCB 9 slot (for Altair/IMSAI)
$30.00
MITS ALTAIR 8800 Original Vintage Microcomputer with 14 boards - Buy It Now
$9500.00
Altair MITS 8800 CPU Parts Kit not IMSAI 8080 S100 (board NOT included)
$64.95
MITS ALTAIR 8800 Original Vintage Microcomputer S-100 Buy It Now $5999
$5999.00
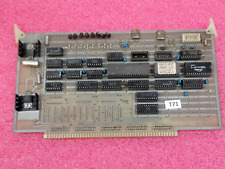
Vintage Altair 8088 CPU Wire Wrapped S100 Card w Mon EPROM circuit board #T71
$99.00
1974 Early Microcomputers by MITS Altair 8800's Ed Roberts HP-9810 Mark-8 Scelbi
$55.00
|
||
|
No Discussions have been posted on this vulnerability. |