|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA587] DSA-587-1 freeamp Vulnerability Assessment Details
|
[DSA587] DSA-587-1 freeamp |
||
|
DSA-587-1 freeamp Detailed Explanation for this Vulnerability Assessment Luigi Auriemma discovered a buffer overflow condition in the playlist module of freeamp which could lead to arbitrary code execution. Recent versions of freeamp were renamed into zinf. For the stable distribution (woody) this problem has been fixed in version 2.1.1.0-4woody2. For the unstable distribution (sid) this problem does not exist in the zinf package as the code in question was rewritten. We recommend that you upgrade your freeamp packages. Solution : http://www.debian.org/security/2004/dsa-587 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

$3200.00
Vintage Atari 1040STf Computer with Mouse and Box, Minimal Testing, Pls Read
$149.99
VINTAGE 1986 ATARI SC1224 12" COLOR MONITOR W/ CABLE FOR ST COMPUTERS
$100.00
Vintage Atari Megafile 44 External 44MB Drive ST STE Mega
$340.00
Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
ATARI 4 Meg STACY ST (For Parts)
$500.00
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
Atari 400/800/XL/XE Computer SIO2PC - PC/Mac Disk Drive Emulator Adapter/Device
$15.25
ATARI Home Computers HOME FILING MANAGER Software **SEALED NEW** 1982
$25.00
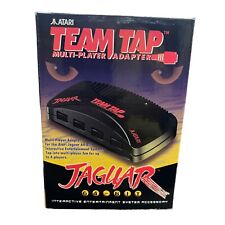
TEAM TAP Atari Jaguar Multi Player Adapter NEW In Box
$25.46
|
||
|
No Discussions have been posted on this vulnerability. |