|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA1008] DSA-1008-1 kdegraphics Vulnerability Assessment Details
|
[DSA1008] DSA-1008-1 kdegraphics |
||
|
DSA-1008-1 kdegraphics Detailed Explanation for this Vulnerability Assessment Marcelo Ricardo Leitner noticed that the current patch in DSA 932 (CVE-2005-3627) for kpdf, the PDF viewer for KDE, does not fix all buffer overflows, still permiting a possible hacker to execute arbitrary code. The old stable distribution (woody) does not contain kpdf packages. For the stable distribution (sarge) this problem has been fixed in version 3.3.2-2sarge4. The unstable distribution (sid) is not affected by this problem. We recommend that you upgrade your kpdf package. Solution : http://www.debian.org/security/2006/dsa-1008 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is (C) 2006 Michel Arboi |
||
|
Cables, Connectors |

Vintage The Print Shop Ensemble III Windows 95 W/worn Box Broderbund
$29.99
Vintage Keytronic PC/AT VT Switch FCC ID:CIG8AVE03435 TESTED WORKING
$30.00
NMB KEYBOARD RT2258TW NMB PS/2 BEIGE 121944-101 REV A VINTAGE NEW OLD STOCK
$25.99
Vintage Apple Macintosh Quadra Computer Incomplete READ
$299.00
Adobe PageMill 2.0 Macintosh 3 Floppy Drives & Cd Vintage Guide Included
$19.96
Vintage Apple MacWorld Magazine Mousepad
$15.00
Vintage Apple Support Tools Mousepad
$15.00
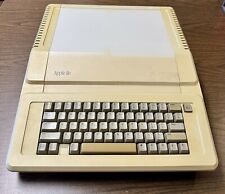
Apple IIe A2S2064 Vintage Personal Computer 128K Enhanced
$200.00
NCR Mechanical Clicky Keyboard Vintage H0150-STD1-12-17 Rare (2 Missing Keys)
$179.00
VINTAGE APPLE POWER MACINTOSH 6500/250 DESKTOP COMPUTER POWERPC BOOTS
$249.50
|
||
|
No Discussions have been posted on this vulnerability. |