|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Databases >> DB2 < 9 Fixpack 2 Vulnerability Assessment Details
|
DB2 < 9 Fixpack 2 |
||
|
Checks DB2 signature Detailed Explanation for this Vulnerability Assessment Summary : The remote database server is affected by multiple issues. Description : According to its version, the installation of DB2 on the remote host permits unsafe access to several setuid-root binaries. A local user may be able to leverage this to crash the affected database server or possibly even gain root-level access. In addition, the fenced userid may be able to access directories without proper authorization. See also : http://labs.idefense.com/intelligence/vulnerabilities/display.php?id=480 http://labs.idefense.com/intelligence/vulnerabilities/display.php?id=481 http://archives.neohapsis.com/archives/fulldisclosure/2007-02/0521.html http://archives.neohapsis.com/archives/fulldisclosure/2007-02/0523.html http://www-1.ibm.com/support/docview.wss?uid=swg21255745 http://www-1.ibm.com/support/docview.wss?uid=swg21255747 http://www-1.ibm.com/support/docview.wss?uid=swg1IY86711 Solution : Apply DB2 Version 9 FixPak 2 or later. Network Security Threat Level: High / CVSS Base Score : 7.0 (AV:L/AC:L/Au:NR/C:C/I:C/A:C/B:N) Networks Security ID: 22677, 22729 Vulnerability Assessment Copyright: This script is Copyright (C) 2007 Tenable Network Security |
||
|
Cables, Connectors |

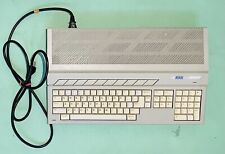
Vintage Atari 1040STf Computer with Mouse and Box, Minimal Testing, Pls Read
$149.99
Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
Atari 400/800/XL/XE Computer SIO2PC - PC/Mac Disk Drive Emulator Adapter/Device
$15.25
Atari Mega STE or TT Keyboard. Used. Untested.
$300.00
Paper Clip Word Processor Floppy Disk -Commodore 64 / Atari 800XL / 65XE / 130XE
$19.99
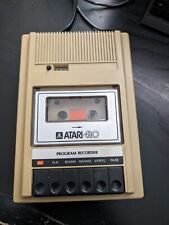
Atari 410 Program Cassette Recorder Clean Tested for power/4 cassettes/Cover
$22.99
Rare Vintage Collectible Original Atari 800 Home Computer With Case - UNTESTED
$219.99
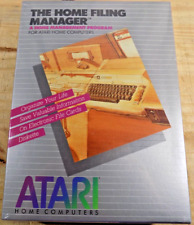
ATARI Home Computers HOME FILING MANAGER Software **SEALED NEW** 1982
$25.00
Rare Vintage Atari XF551 Floppy Disk Drive Station for 400, 800, 600, XE and XL
$300.00
|
||
|
No Discussions have been posted on this vulnerability. |