|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> Bizmail.cgi Mail From Unauthorized Mail Relay Vulnerability Vulnerability Assessment Details
|
Bizmail.cgi Mail From Unauthorized Mail Relay Vulnerability |
||
|
Checks the version of bizmail.cgi Detailed Explanation for this Vulnerability Assessment The remote web server is hosting the CGI bizmail.cgi, a CGI application which sends web forms to email addresses. The remote version of this software is vulnerable to a flaw which may permit a possible hacker to use the remote CGI as a mail relay. A spammer may exploit this flaw to send emails anonymously. Solution: Upgrade to Bizmail 2.2 or newer Network Security Threat Level: High Networks Security ID: 12620 Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

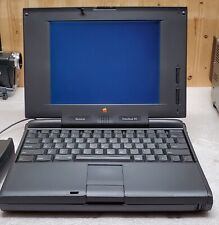
Apple Mac Powerbook Duo 230 Vintage Laptop
$60.00
Vintage Apple Macintosh SE Case - Empty Shell - Housing retro project
$60.00
Vintage Apple Macintosh II 2 M5000 Computer no power very nice w drives card
$350.00
Vintage Apple Macintosh Powerbook 190 Series M3047 Laptop Parts/Repair
$69.00
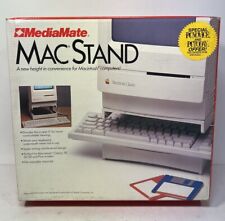
Vintage MediaMate Early 90’s Macintosh Mac Desktop PC Home Computer Stand #18200
$50.00
VINTAGE REFURBISHED MACINTOSH SE WITH BLUESCSI RECAPPED POWER SUPPLY
$300.00
Apple Mac IIsi computer Very Good condition Vintage
$100.00
Apple Studio Display Monitor M2454 15" vintage Mac LCD
$80.00
Vintage Apple Power Macintosh PC Computer M3979 7600/132
$249.50
Vintage Apple Macintosh Quadra Computer Incomplete READ
$299.00
|
||
|
No Discussions have been posted on this vulnerability. |