|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Misc. >> Airport Administrative Port Vulnerability Assessment Details
|
Airport Administrative Port |
||
|
Connects to port 5009 and says 'Hello' Detailed Explanation for this Vulnerability Assessment The remote host is an Apple Airport Wireless Access Point which can be administrated on top of TCP port 5009. There is a design flaw in the administrative protocol which makes the clients which connect to this port send the password in plain text (although slightly obsfuscated). A possible hacker who has the ability to sniff the data going to this device may use this flaw to gain its administrative password and gain its control. Since the airport base station does not keep any log, it will be difficult to acertain that administrative access has been stolen. Solution : Block incoming traffic to this port, and only administer this base station when connected to it using a cross-over ethernet cable. Network Security Threat Level: Medium Networks Security ID: 7554 Vulnerability Assessment Copyright: This script is Copyright (C) 2003-2007 Tenable Network Security |
||
|
Cables, Connectors |

Vintage Cardco Vic-20, C64, C16, and C128 Parallel Printer Interface Card - New
$19.99
Vintage Microsoft Office 2000 Premium 4 CDs + Product Keys + Service Pack CD
$59.99
Vintage CARDCO Vic-20 C64 +4 C16 and C128 Parallel Printer Interface Card - QTY
$19.99
Intel Pentium A80502-166 Vintage CPU | UNTESTED - READ DESCRIPTION
$19.55
Apple Desktop Bus Mouse I ADB Beige Vintage for Macintosh G5431 M0142 A9M0331
$23.99
(5) Vintage DiskBank floppy Disk Storage Holders Vintage
$29.95
ROCKWELL SCIENTIFIC SLIDE RULE 31R CALCULATOR VINTAGE UNTESTED
$24.24
NMB KEYBOARD RT2258TW NMB PS/2 BEIGE 121944-101 REV A VINTAGE NEW OLD STOCK
$25.99
Vintage 1986 IBM 1389262 Model M buckling spring terminal keyboard -1 keycap
$150.00
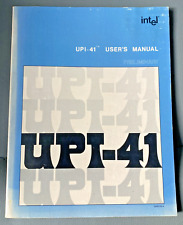
Vintage Intel UPI-41 Universal Peripheral Interface User's Manual
$24.99
|
||
|
No Discussions have been posted on this vulnerability. |