|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SuSE Local Security Checks >> SUSE-SA:2005:068: kernel Vulnerability Assessment Details
|
SUSE-SA:2005:068: kernel |
||
|
Check for the version of the kernel package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory SUSE-SA:2005:068 (kernel). The Linux kernel was updated to fix several security problems and several bugs, listed below: Security fixes: - CVE-2005-3783: A check in ptrace(2) handling that finds out if a process is attaching to itself was incorrect and could be used by a local attacker to crash the machine. (All) - CVE-2005-3784: A check in reaping of terminating child processes did not consider ptrace(2) attached processes and would leave a ptrace reference dangling. This could lead to a local user being able to crash the machine. (Linux kernel 2.6 based products only) - CVE-2005-3806: A bug in IPv6 flow label handling code could be used by a local attacker to free non-allocated memory and in turn corrupt kernel memory and likely crash the machine. (All) - CVE-2005-3805: A locking problem in POSIX timer handling could be used by a local attacker on a SMP system to deadlock the machine. (SUSE Linux 9.3) - CVE-2005-3527: A race condition in do_coredump in signal.c permits local users to cause a denial of service (machine hang) by triggering a core dump in one thread while another thread has a pending SIGSTOP. (SUSE Linux 9.3) - CVE-2005-3807: A memory kernel leak in VFS lease handling can exhaust the machine memory and so cause a local denial of service. This is seen in regular Samba use and could also be triggered by local attackers. (SUSE Linux 9.3) - Others: see original advisory Solution : http://www.suse.de/security/advisories/2005_68_kernel.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

ASUS H110M-R Motherboard Intel 6th/7th Gen LGA1151 DDR4 Micro-ATX i/o shield
$42.00
***NEW*** BCM RX67Q Gaming Motherboard | Intel Q67 2nd/3rd Gen. | LGA1155 | DDR3
$29.77
***NEW*** BCM RX67Q mATX Gaming Motherboard Combo | Intel i5-3470 | 16GB DDR3
$49.77
Micro ATX Desktop Motherboard ASUS H110M-C LGA 1151
$31.95
Asrock Z390 Phantom Gaming 4S/AC Wifi 8th/9th Gen Intel 1151 Motherboard Bulk
$47.39
Gigabyte AMD B550 UD AC Gaming Motherboard - AMD B550 Chipset - AM4 Socket - AMD
$89.99
ASUS Prime Z390-A LGA 1151 Intel Z390 SATA USB 3.1 ATX Motherboard NO I/O
$99.00
MSI B450M PRO-VDH MAX AM4 AMD B450 USB3.2 Micro-ATX Motherboard
$67.99
Asus C204EE Chromebook 4G 32GB Motherboard 60NX02A0-MBG010 90NX02A0-R07003
$79.99
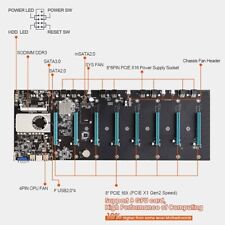
BTC-S37 Mining Motherboard Kit /w SSD & Ram Preinstalled
$59.99
|
||
|
No Discussions have been posted on this vulnerability. |