|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SuSE Local Security Checks >> SUSE-SA:2004:021: php4/mod_php4 Vulnerability Assessment Details
|
SUSE-SA:2004:021: php4/mod_php4 |
||
|
Check for the version of the php4/mod_php4 package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory SUSE-SA:2004:021 (php4/mod_php4). PHP is a well documented, widely-used scripting language often used within web server setups. Stefan Esser found a problem with the 'memory_limit' handling of PHP which permits remote attackers to execute arbitrary code as the user running the PHP interpreter. This problem has been fixed. Additionally a problem within the 'strip_tags' function has been found and fixed which permited remote attackers to inject arbitrary tags into certain web browsers, issuing XSS related attacks. Since there is no easy workaround except disabling PHP, we recommend an update for users running the PHP interpreter within the apache web server. To be sure the update takes effect you have to restart the apache process by executing the following command as root: /usr/sbin/rcapache restart or if you use the apache2 package /usr/sbin/rcapache2 restart Please download the update package for your distribution and verify its integrity by the methods listed in section 3) of this announcement. Then, install the package using the command 'rpm -Fhv file.rpm' to apply the update. Solution : http://www.suse.de/security/2004_21_php4.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

OEM Apple MacBook Pro 13 A1706 A1708 2017 LCD Screen Display Assembly Silver
$128.24
A1382 Genuine OEM Battery for Apple MacBook Pro Unibody 15" A1286 2011 2012 NEW
$35.50
A1819 Genuine OEM Battery for APPLE MacBook Pro 13" A1706 MLH12LL/A MPXV2LL/A
$48.79
A1383 New Genuine OEM Battery for Apple MacBook Pro 17" A1297 Early/Late 2011 US
$45.50
Genuine Apple A1718 61W USB-C Power Adapter Apple OEM CHARGER
$24.99
Apple OEM Original (A1374) 45W MagSafe Power Adapter with Fold Plug Only - White
$10.95
OEM 61W USB C Type C Adapter Charger for Apple MacBook PRO 13" A1718 + Cable NEW
$23.00
APPLE OEM Original Cinema Display (Aluminum) Power Supply AC Adapter 65w or 90w
$18.99
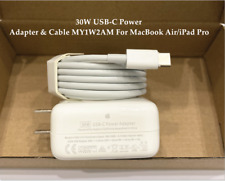
OEM 30W USB-C Power Adapter Charger for apple MacBook Air iPhone 11 12 Pro +Cord
$22.89
GENUINE Apple OEM A1096 Cinema Display Power Adapter 65W with power cord Tested
$17.95
|
||
|
No Discussions have been posted on this vulnerability. |