|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SuSE Local Security Checks >> SUSE-SA:2003:025: samba Vulnerability Assessment Details
|
SUSE-SA:2003:025: samba |
||
|
Check for the version of the samba package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory SUSE-SA:2003:025 (samba). Digital Defense Inc. have discovered a buffer overflow in the samba file server, the widely spread implementation of the SMB protocol. The flaw permits a remote attacker to execute arbitrary commands as root on a server that runs a vulnerable version of samba. The vulnerability is known as DDI trans2.c overflow bug and is assigned the CVE ID CVE-2003-0201. Since this vulnerability was found during an analysis of an exploit happening in the wild, it should be assumed that exploits are circulating in the internet. A possible workaround is to restrict access using the 'hosts permit' directive in the smb.conf file to a group of trusted hosts/addresses that should be able to access the server. Please see the sbm.conf(5) manpage ('man smb.conf') for more details about such configuration changes. It should be noted that each change of the configuration requires restarting/reloading the samba daemon ('rcsmb reload'). The only efficient and permanent remedy for the vulnerability should be to install the provided update packages from locations as listed below. It should be noted that this announcement is not a re-release of Solution : http://www.suse.de/security/2003_025_samba.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

Vintage Apple Macintosh II 2 M5000 Computer no power very nice w drives card
$350.00
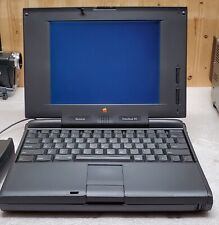
Apple Mac Powerbook Duo 230 Vintage Laptop
$60.00
Apple MacIntosh IIcx Vintage Desktop Computer M5650 - 1988/89
$200.00
Vintage Apple Macintosh SE Case - Empty Shell - Housing retro project
$60.00
VINTAGE REFURBISHED MACINTOSH SE WITH BLUESCSI RECAPPED POWER SUPPLY
$300.00
Vintage Apple Macintosh Powerbook 190 Series M3047 Laptop Parts/Repair
$69.00
VINTAGE RARE POWER R 2703 VIDEO ADAPTER FOR MACINTOSH SE SE/30 LCD NOT INCLUDED
$300.00
Apple Macintosh Vintage DOS on Mac PC Compatible Interface PCI 590-4539 Y Cable
$80.00
Apple Macintosh SE/30 M5119 Vintage Mac Computer BAD FLOPPY DRIVE FOR PARTS
$350.00
APPLE MACINTOSH PLUS M0001A Vintage Mac Computer Tested Working
$799.99
|
||
|
No Discussions have been posted on this vulnerability. |