|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SuSE Local Security Checks >> SUSE-SA:2002:036: mod_php4 Vulnerability Assessment Details
|
SUSE-SA:2002:036: mod_php4 |
||
|
Check for the version of the mod_php4 package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory SUSE-SA:2002:036 (mod_php4). PHP is a well documented and widely used web programming language. If a PHP script runs in 'safe mode' several restrictions are applied to it including limits on execution of external programs. A possible hacker can pass shell meta-characters or sendmail(8) command line options via the 5th argument (introduced in version 4.0.5) of the mail() function to execute shell commands or control the behavior of sendmail(8). The CRLF injection vulnerabilities in fopen(), file(), header(), ... permit a possible hacker to bypass ACLs or trigger cross-side scripting. The mod_php4 package is not installed by default. A temporary fix is not known. Please note, that the following packages were rebuild too: - mod_php4-core - mod_php4-aolserver - mod_php4-devel - mod_php4-servlet - mod_php4-roxen Please download the update package for your distribution and verify its integrity by the methods listed in section 3) of this announcement. Then, install the package using the command 'rpm -Fhv file.rpm' to apply the update. Solution : http://www.suse.de/security/2002_036_modphp4.html Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

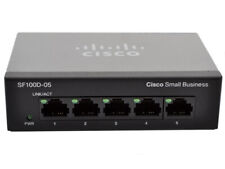
Cisco (SG100D-05-UK) 5-Ports External Ethernet Switch
$40.00
Cisco SG110 24 Port Gigabit Ethernet Switch w/ 2 x SFP SG110-24
$117.00
Cisco 110 SG110D-05 5 Ports Ethernet Switch - 1000Base-X SG110D-05-EU-WS
$40.00
Cisco SG95-16 16-Port Gigabit Switch SG95-16-SG
$47.00
Juniper Networks EX3300-48P 48-Port PoE+ 4x SFP+ Network Switch w/ Power Cord
$43.95
New Linksys SE3005 5-port Gigabit Ethernet Switch
$18.99
New 10/100 Mbps 8 Ports Fast Ethernet LAN Desktop RJ45 Network Switch Hub
$11.49
Linksys SE3008 8 Ports Rack Mountable Gigabit Ethernet Switch
$21.99
Fortinet FortiSwitch FS-124D-POE 24 Port Gigabit Ethernet Switch UNREGISTERED
$99.97
Netgear Prosafe Plus JGS524PE 24 Port Gigabit Switch 12 Port PoE JGS524PE-100NAS
$129.98
|
||
|
No Discussions have been posted on this vulnerability. |