|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2006-0574: kernel Vulnerability Assessment Details
|
RHSA-2006-0574: kernel |
||
|
Check for the version of the kernel packages Detailed Explanation for this Vulnerability Assessment Updated kernel packages that fix a privilege escalation security issue in the Red Hat Enterprise Linux 4 kernel are now available. This security advisory has been rated as having important security impact by the Red Hat Security Response Team. The Linux kernel handles the basic functions of the operating system. During security research, Red Hat discovered a behavioral flaw in core dump handling. A local user could create a program that would cause a core file to be dumped into a directory they would not normally have permissions to write to. This could lead to a denial of service (disk consumption), or permit the local user to gain root rights. (CVE-2006-2451) Prior to applying this update, users can remove the ability to escalate rights using this flaw by configuring core files to dump to an absolute location. By default, core files are created in the working directory of the faulting application, but this can be overridden by specifying an absolute location for core files in /proc/sys/kernel/core_pattern. To avoid a potential denial of service, a separate partition for the core files should be used. All Red Hat Enterprise Linux 4 users are advised to upgrade their kernels to the packages associated with their machine architectures and configurations as listed in this erratum. Solution : http://rhn.redhat.com/errata/RHSA-2006-0574.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

Dell PowerEdge R640 Server | 2x Gold 6132 28 Cores | H730p | Choose RAM / DRIVES
$2630.00
### MZ-7KE1T0 Samsung 850 Pro Series 1TB 2.5 inch SATA3 SSD ###
$105.00
M.2 NVME SATA SSD Enclosure USB 3.2 Gen 2 10Gbps for M-Key or M+B Key SSD to 8TB
$19.86
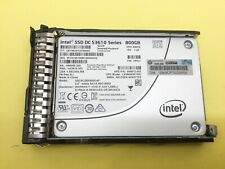
804625-B21 HPE 800GB SATA 6G MIXED USE SFF (2.5IN) SC SSD 805381-001
$67.00
Patriot P210 128GB 256GB 512GB 1TB 2TB 2.5" SATA 3 6GB/s Internal SSD PC/MAC Lot
$19.99
Intel DC S3510 Series 120GB SSD 2.5" 6Gb/s SATA Solid State Drive SSDSC2BB120G6K
$9.99
Micron 5100 MAX 120GB SATA 6Gb/s 2.5" Internal SSD MTFDDAK120TCC Solid State
$9.99
Western Digital PC SN730 256GB NVMe SDBQNTY-256G M.2 2280 PCIe Solid State (SSD)
$16.00
Netac 1TB 2TB 512GB Internal SSD 2.5'' SATA III 6Gb/s Solid State Drive lot
$109.99
Fanxiang SSD 4TB 2TB 1TB PS5 SSD M.2 NVME SSD 7300MBS PCIe 4.0 Solid State Drive
$249.99
|
||
|
No Discussions have been posted on this vulnerability. |