|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2003-074: sendmail Vulnerability Assessment Details
|
RHSA-2003-074: sendmail |
||
|
Check for the version of the sendmail packages Detailed Explanation for this Vulnerability Assessment Updated Sendmail packages are available to fix a vulnerability that may permit remote attackers to gain root rights by sending a carefully crafted message. [Updated March 18 2003] Added packages for Red Hat Enterprise Linux ES and Red Hat Enterprise Linux WS. Sendmail is a widely used Mail Transport Agent (MTA) which is included in all Red Hat Enterprise Linux distributions. During a code audit of Sendmail by ISS, a critical vulnerability was uncovered that affects unpatched versions of Sendmail prior to version 8.12.8. A remote attacker can send a carefully crafted email message which, when processed by sendmail, causes arbitrary code to be executed as root. We are advised that a proof-of-concept exploit is known to exist, but is not believed to be in the wild. Since this is a message-based vulnerability, MTAs other than Sendmail may pass on the carefully crafted message. This means that unpatched versions of Sendmail inside a network could still be at risk even if they do not accept external connections directly. All users are advised to update to these erratum packages which contain a backported patch to correct this vulnerability. Red Hat would like to thank Eric Allman for his assistance with this vulnerability. Solution : http://rhn.redhat.com/errata/RHSA-2003-074.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

ASUS H110M-R Motherboard Intel 6th/7th Gen LGA1151 DDR4 Micro-ATX i/o shield
$42.00
***NEW*** BCM RX67Q Gaming Motherboard | Intel Q67 2nd/3rd Gen. | LGA1155 | DDR3
$29.77
Micro ATX Desktop Motherboard ASUS H110M-C LGA 1151
$31.95
Asrock Z390 Phantom Gaming 4S/AC Wifi 8th/9th Gen Intel 1151 Motherboard Bulk
$47.55
ASUS Prime Z390-A LGA 1151 Intel Z390 SATA USB 3.1 ATX Motherboard NO I/O
$99.00
MSI B450M PRO-VDH MAX AM4 AMD B450 USB3.2 Micro-ATX Motherboard
$67.99
MSI A320M-A PRO AM4 AMD A320 USB3.2 Gen1 Micro-ATX Motherboard
$46.99
ASUS Prime Q270M-C LGA1151 DP HDMI VGA SATA 6GB/s USB 3.0 MicroATX Motherboard
$34.19
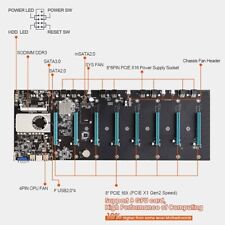
BTC-S37 Mining Motherboard Kit /w SSD & Ram Preinstalled
$59.99
GIGABYTE MB10-Datto Motherboard Xeon D-1521- SR2DF 2.40 GHz- Open Box
$121.50
|
||
|
No Discussions have been posted on this vulnerability. |