|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2002-137: util Vulnerability Assessment Details
|
RHSA-2002-137: util |
||
|
Check for the version of the util packages Detailed Explanation for this Vulnerability Assessment The util-linux package shipped with Red Hat Linux Advanced Server contains a locally exploitable vulnerability. The util-linux package contains a large variety of low-level system utilities that are necessary for a Linux system to function. The 'chfn' utility included in this package permits users to modify personal information stored in the system-wide password file, /etc/passwd. In order to modify this file, this application is installed setuid root. Under certain conditions, a carefully crafted attack sequence can be performed to exploit a complex file locking and modification race present in this utility permiting changes to be made to /etc/passwd. In order to successfully exploit the vulnerability and perform privilege escalation there is a need for a minimal administrator interaction. Additionally, the password file must be over 4 kilobytes, and the local attackers entry must not be in the last 4 kilobytes of the password file. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2002-0638 to this issue. An interim workaround is to remove setuid flags from /usr/bin/chfn and /usr/bin/chsh. All users of Red Hat Linux should update to the errata util-linux packages which contain a patch to correct this vulnerability. Many thanks to Michal Zalewski of Bindview for alerting us to this issue. Solution : http://rhn.redhat.com/errata/RHSA-2002-137.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

***NEW*** BCM RX67Q Gaming Motherboard | Intel Q67 2nd/3rd Gen. | LGA1155 | DDR3
$29.77
ASUS H110M-R Motherboard Intel 6th/7th Gen LGA1151 DDR4 Micro-ATX i/o shield
$42.00
GIGABYTE B560M DS3H AC LGA1200 Intel B560 SATA 6Gb/s Micro ATX Intel Motherboard
$64.99
Asus Prime H310M-A R2.0 Intel LGA 1151 DDR4 Desktop Motherboard
$46.99
MSI B450M PRO-VDH MAX AM4 AMD B450 USB3.2 Micro-ATX Motherboard
$67.99
Micro ATX Desktop Motherboard ASUS H110M-C LGA 1151
$31.95
Gigabyte AMD B550 UD AC Gaming Motherboard - AMD B550 Chipset - AM4 Socket - AMD
$89.99
Asus Prime B250M-C Motherboard Supports DDR4 Intel 7th Gen
$39.99
GIGABYTE MB10-Datto Motherboard Xeon D-1521- SR2DF 2.40 GHz- Open Box
$112.00
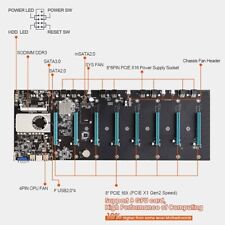
BTC-S37 Mining Motherboard Kit /w SSD & Ram Preinstalled
$59.99
|
||
|
No Discussions have been posted on this vulnerability. |