|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Settings >> NIDS evasion Vulnerability Assessment Details
|
NIDS evasion |
||
|
NIDS evasion options Detailed Explanation for this Vulnerability Assessment This test configures Nessus for NIDS evasion (see the 'Prefs' panel). NIDS evasion options are useful if you want to acertain the quality of the expensive NIDS you just bought. TCP Evasion techniques : - Split : send data one byte at a time. This confuses NIDSes which do not perform stream reassembly - Injection : same as split, but malformed TCP packets containing bogus data are sent between normal packets. Here, a 'malformed' tcp packet means a legitimate TCP packet with a bogus checksum. This confuses NIDSes which perform stream reassembly but do not accurately verify the checksum of the packets or which do not acertain if the remote host actually receives the packets seen - Short TTL : same as split, but a valid TCP packets containing bogus data are sent between normal packets. These packets have a short (N-1), meaning that if the NIDS is on a gateway, it will see these packets go through, but they will not reach the target host. This confuses NIDSes which perform stream reassembly but do not accurately check if the packet can actually reach the remote host or which do not acertain if the remote host actually receives the packets seen - Fake RST : each time a connection is established, Nessus will send a RST packet with a bogus tcp checksum or a bogus ttl (depending on the options you chose above), thus making the IDS believe the connection was closed abruptly. This confuses badly written NIDSes which believe anything they see. Warning: those features are experimental and some options may result in false negatives! This test does not do any security check. Network Security Threat Level: None Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2002 Michel Arboi / Renaud Deraison |
||
|
Cables, Connectors |

Lot of 10pcs Brocade 57-1000012-01 8Gbps SWL 850nm SFP+ Optical Transceivers
$19.00
Cisco GLC-FE-100LX 100BASE-LX SFP Transceiver Module
$15.59
Cisco GLC-FE-100LX-RGD 100BASE-LX SFP Transceiver Module
$17.99
Cisco Meraki MA-SFP-1GB-SX 1000BASE-SX SFP Transceiver Module
$24.99
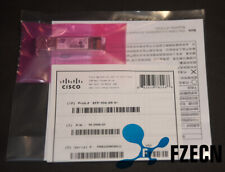
Genuine Cisco SFP-10G-SR V03 10GBASE-SR SFP+ Transceiver Module 10-2415-03
$8.00
SFP-10G-SR Original Cisco 10GBASE-SR SFP+ V02 Multi mode Transceiver 10-2415-02
$5.00
Brand New Cisco GLC-LH-SMD 1000BASE-LX/LH SFP Module 1310nm 10km SMF LC
$13.89
Lot of 10 - HP 10Gb SR SFP+ Transceiver 455883-B21 455885-001 456096-001 850nm
$23.99
LOT OF 20 Genuine Cisco SFP-10G-SR V03 10GBASE-SR SFP+ Transceiver Module
$89.00
NEW Sealed Cisco SFP-10G-SR-S 10G SR SFP+ Module 850nmMM *US Shipping*
$15.00
|
||
|
No Discussions have been posted on this vulnerability. |