|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gain root remotely >> MailEnable IMAP Server Buffer Overflow and Directory Traversal Vulnerabilities Vulnerability Assessment Details
|
MailEnable IMAP Server Buffer Overflow and Directory Traversal Vulnerabilities |
||
|
Checks for buffer overflow and directory traversal vulnerabilities in MailEnable IMAP server Detailed Explanation for this Vulnerability Assessment Summary : The remote IMAP server is affected by buffer overflow and directory traversal vulnerabilities. Description : The remote host is running MailEnable, a commercial mail server for Windows. The IMAP server bundled with the version of MailEnable Professional or Enterprise Edition installed on the remote host is prone to a stack-based buffer overflow when handling an overly-long mailbox name in certain commands. An authenticated attacker may be able to leverage this issue to execute arbitrary code remotely as the SYSTEM user. It also fails to filter directory traversal sequences from mailbox names passed to the 'CREATE' and 'RENAME' commands. An authenticated attacker can exploit these issues to create arbitrary directories on the affected host and to cause a denial of service by renaming the mail directories of other users. See also : http://secunia.com/secunia_research/2005-59/advisory/ http://www.mailenable.com/hotfix/ Solution : Upgrade to MailEnable Professional 1.7 or later. Or apply ME-100008, the IMAP Cumulative Hotfix dated November 18th, 2005, referenced in the vendor URL above. Network Security Threat Level: High / CVSS Base Score : 7.0 (AV:R/AC:L/Au:NR/C:P/I:P/A:P/B:N) Networks Security ID: 15492, 15494 Vulnerability Assessment Copyright: This script is Copyright (C) 2005-2006 Tenable Network Security |
||
|
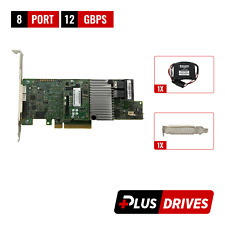
Cables, Connectors |

LSI 9305-16i SATA SAS 12Gbs RAID Controller PCIe 3.0 x8 IT-Mode 4* 8643 SATA
$229.99
ACASIS 2.5/3.5 inch 2 Bay SATA USB 3.0 Hard Drive Disk HDD SSD Enclosure 4 RAID
$58.99
Dell R630 8SFF 2.4Ghz 12-Core 128GB H330 RAID 10GB RJ-45 NIC 2x750W PSU 8x Trays
$430.04
Dell R630 8SFF 2.6Ghz 28-Core 128GB H330 RAID 10GB RJ-45 NIC 2x750W PSU 8x Trays
$490.04
Inspur LSI 9300-8i Raid Card 12Gbps HBA HDD Controller High Profile IT MODE
$15.98
LSI MegaRAID 9361-8i 12Gb PCIe 8-Port SAS/SATA RAID 1Gb w/BBU/CacheVault/License
$39.95
ORICO Multi Bay RAID Hard Drive Enclosure USB 3.0/ Type-C For 2.5/3.5'' HDD SSDs
$82.49
LSI MegaRAID 9361-8i 12Gbps PCIe 3 x8 SATA SAS 3 8 Port RAID + BBU & CacheVault
$39.00
2 Bay RAID Hard Drive Enclosure USB 3.0 Type-B for 2.5" SATA SSD/HDD Enclosure
$59.99
Dell PERC H330 PCIe 3.0 x8 RAID Storage Controller 04Y5H1 High Profile
$17.99
|
||
|
No Discussions have been posted on this vulnerability. |