|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200511-07] OpenVPN: Multiple vulnerabilities Vulnerability Assessment Details
|
[GLSA-200511-07] OpenVPN: Multiple vulnerabilities |
||
|
OpenVPN: Multiple vulnerabilities Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200511-07 (OpenVPN: Multiple vulnerabilities) The OpenVPN client contains a format string bug in the handling of the foreign_option in options.c. Furthermore, when the OpenVPN server runs in TCP mode, it may dereference a NULL pointer under specific error conditions. Impact A remote attacker could setup a malicious OpenVPN server and trick the user into connecting to it, potentially executing arbitrary code on the client's computer. A remote attacker could also exploit the NULL dereference issue by sending specific packets to an OpenVPN server running in TCP mode, resulting in a Denial of Service condition. Workaround Do not use "pull" or "client" options in the OpenVPN client configuration file, and use UDP mode for the OpenVPN server. References: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-3393 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-3409 http://openvpn.net/changelog.html Solution: All OpenVPN users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=net-misc/openvpn-2.0.4" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

MOS 6502 CPU for Commodore VIC 20 Computer & 1541 & 1571 Tested US SELLER
$12.99
$200.00
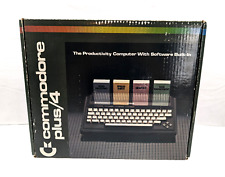
Commodore Plus 4 Computer Complete In Box (Tested Works)
$180.00
Commodore Amiga FLOPPY DRIVE EMULATOR GOTEK BLACK - WORKING
$37.95
Commodore Amiga FLOPPY DRIVE EMULATOR GOTEK - WORKING
$34.95
$240.00
commodore 128, 128D, 128DCR A/V Breakout
$19.99
Commodore SX-64 W/Rare 1541 Flash Installed READ DESCRIPTION SX64 C-64
$459.00
TeensyROM Cartridge for Commodore 64/128: MIDI, Fastload, Emulation, and Network
$65.00
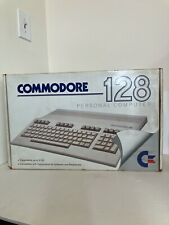
Vintage Commodore 128 Personal Computer w/Box 1987 Untested As Is Rare
$249.99
|
||
|
No Discussions have been posted on this vulnerability. |