|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200508-08] Xpdf, Kpdf, GPdf: Denial of Service vulnerability Vulnerability Assessment Details
|
[GLSA-200508-08] Xpdf, Kpdf, GPdf: Denial of Service vulnerability |
||
|
Xpdf, Kpdf, GPdf: Denial of Service vulnerability Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200508-08 (Xpdf, Kpdf, GPdf: Denial of Service vulnerability) Xpdf, Kpdf and GPdf do not handle a broken table of embedded TrueType fonts correctly. After detecting such a table, Xpdf, Kpdf and GPdf attempt to reconstruct the information in it by decoding the PDF file, which causes the generation of a huge temporary file. Impact A remote attacker may cause a Denial of Service by creating a specially crafted PDF file, sending it to a CUPS printing system (which uses Xpdf), or by enticing a user to open it in Xpdf, Kpdf, or GPdf. Workaround There is no known workaround at this time. References: http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-2097 Solution: All Xpdf users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=app-text/xpdf-3.00-r10" All GPdf users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=app-text/gpdf-2.10.0-r1" All Kpdf users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=kde-base/kdegraphics-3.3.2-r3" All KDE Split Ebuild Kpdf users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=kde-base/kpdf-3.4.1-r1" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

AUDIO CODES MP-114 VOIP Gateway Open Box
$24.99
Cisco CP-8832-K9 Unified 8800 Series Conference VOIP IP Phone 1 Year Warranty
$139.00
$199.99
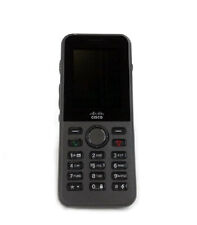
Cisco CP-8821-K9 8821 Wireless VOIP IP Phone 1 Year Waranty
$330.00
Yealink W73H IP DECT VOIP Phone
$10.00
New Cisco 7945G IP VoIP Gigabit GIGE Telephone Phone CP-7945G -
$24.95
Cisco CP-7945G VOIP Phone With Stand & Handset Business IP Phone 7945
$3.00
Yealink T54W IP Phone, 16 VoIP Accounts. 4.3-Inch Color Display - Black
$99.99
Grandstream GS-HT802 2 Port Analog Telephone Adapter VoIP Phone & Device, Black
$32.00
Cisco VG202XM Analog Voice Gateway VoIP -- [NEW/FULL KIT]
$76.00
|
||
|
No Discussions have been posted on this vulnerability. |








![Cisco VG202XM Analog Voice Gateway VoIP -- [NEW/FULL KIT] picture](/store/img/g/I0YAAOSwn0lle2WJ/s-l225/Cisco-VG202XM-Analog-Voice-Gateway-VoIP-NEW-FULL-K.jpg)