|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200508-02] ProFTPD: Format string vulnerabilities Vulnerability Assessment Details
|
[GLSA-200508-02] ProFTPD: Format string vulnerabilities |
||
|
ProFTPD: Format string vulnerabilities Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200508-02 (ProFTPD: Format string vulnerabilities) "infamous42md" reported that ProFTPD is vulnerable to format string vulnerabilities when displaying a shutdown message containing the name of the current directory, and when displaying response messages to the client using information retrieved from a database using mod_sql. Impact A remote attacker could create a directory with a malicious name that would trigger the format string issue if specific variables are used in the shutdown message, potentially resulting in a Denial of Service or the execution of arbitrary code with the rights of the user running the ProFTPD server. A possible hacker with control over the database contents could achieve the same result by introducing malicious messages that would trigger the other format string issue when used in server responses. Workaround Do not use the "%C", "%R", or "%U" in shutdown messages, and do not set the "SQLShowInfo" directive. References: http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-2390 Solution: All ProFTPD users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=net-ftp/proftpd-1.2.10-r7" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

ACASIS 2.5/3.5 inch 2 Bay SATA USB 3.0 Hard Drive Disk HDD SSD Enclosure 4 RAID
$58.99
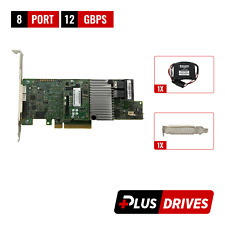
Cisco UCS LSI MegaRAID 9271CV-8I SAS2308 PCIe SAS Internal RAID Controller
$28.00
Intel PCIe SSD AIC RAID Controller Card G97168-252
$44.55
LSI 9207-8i 8-Port SAS Non-RAID 6GBPS PCIe Host Bus Adapter
$34.95
LSI MegaRAID 9361-8i 12Gb PCIe 8-Port SAS/SATA RAID 1Gb w/BBU/CacheVault/License
$39.95
LSI MegaRaid 9361-8i 12Gbps SAS / SATA Raid Controller PCIe x8 3.0 Tested
$29.00
LSI MegaRAID 9361-8i 12Gbps PCIe 3 x8 SATA SAS 3 8 Port RAID + BBU & CacheVault
$39.00
Oracle Sun 8-Port 6 Gbps SAS/SATA Raid Controller PCIe w/Cables 7055240 7047503
$13.49
G TECHNOLOGY G RAID 0G04228 2-Bay Thunderbolt 2 RAID Array W/Power Supply
$99.99
4 Bay RAID External Hard Drive Enclosure for 2.5/3.5" SATA HDD/SSD
$79.99
|
||
|
No Discussions have been posted on this vulnerability. |