|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200507-17] Mozilla Thunderbird: Multiple vulnerabilities Vulnerability Assessment Details
|
[GLSA-200507-17] Mozilla Thunderbird: Multiple vulnerabilities |
||
|
Mozilla Thunderbird: Multiple vulnerabilities Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200507-17 (Mozilla Thunderbird: Multiple vulnerabilities) The following vulnerabilities were found and fixed in Mozilla Thunderbird: "moz_bug_r_a4" and "shutdown" discovered that Thunderbird was improperly cloning base objects (MFSA 2005-56). "moz_bug_r_a4" also reported that Thunderbird was overly trusting contents, permiting privilege escalation via property overrides (MFSA 2005-41, 2005-44), that it failed to validate XHTML DOM nodes properly (MFSA 2005-55), and that XBL scripts ran even when Javascript is disabled (MFSA 2005-46). "shutdown" discovered a possibly exploitable crash in InstallVersion.compareTo (MFSA 2005-50). Andreas Sandblad from Secunia reported that a child frame can call top.focus() even if the framing page comes from a different origin and has overridden the focus() routine (MFSA 2005-52). Georgi Guninski reported missing Install object instance checks in the native implementations of XPInstall-related JavaScript objects (MFSA 2005-40). Finally, Vladimir V. Perepelitsa discovered a memory disclosure bug in JavaScript's regular expression string replacement when using an anonymous function as the replacement argument (CVE-2005-0989 and MFSA 2005-33). Impact A remote attacker could craft malicious email messages that would leverage these issues to inject and execute arbitrary script code with elevated rights or help in stealing information. Workaround There are no known workarounds for all the issues at this time. References: http://www.mozilla.org/projects/security/known-vulnerabilities.html#Thunderbird http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0989 Solution: All Mozilla Thunderbird users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=mail-client/mozilla-thunderbird-1.0.5" All Mozilla Thunderbird binary users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=mail-client/mozilla-thunderbird-bin-1.0.5" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Rare Vintage Collectible Original Atari 800 Home Computer With Case - UNTESTED
$219.99
Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
Paper Clip Word Processor Floppy Disk -Commodore 64 / Atari 800XL / 65XE / 130XE
$19.99
Atari 400/800/XL/XE Computer SIO2PC - PC/Mac Disk Drive Emulator Adapter/Device
$15.25
Atari Mega STE or TT Keyboard. Used. Untested.
$300.00
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
Vintage Atari 800XL Computer With Original Box
$140.00
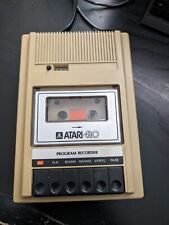
Atari 410 Program Cassette Recorder Clean Tested for power/4 cassettes/Cover
$22.99
Rare Vintage Atari XF551 Floppy Disk Drive Station for 400, 800, 600, XE and XL
$300.00
Atari 400 with program recorder and manual
$199.00
|
||
|
No Discussions have been posted on this vulnerability. |