|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200502-33] MediaWiki: Multiple vulnerabilities Vulnerability Assessment Details
|
[GLSA-200502-33] MediaWiki: Multiple vulnerabilities |
||
|
MediaWiki: Multiple vulnerabilities Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200502-33 (MediaWiki: Multiple vulnerabilities) A security audit of the MediaWiki project discovered that MediaWiki is vulnerable to several cross-site scripting and cross-site request forgery attacks, and that the image deletion code does not sufficiently sanitize input parameters. Impact By tricking a user to load a carefully crafted URL, a remote attacker could hijack sessions and authentication cookies to inject malicious script code that will be executed in a user's browser session in context of the vulnerable site, or use JavaScript submitted forms to perform restricted actions. Using the image deletion flaw, it is also possible for authenticated administrators to delete arbitrary files via directory traversal. Workaround There is no known workaround at this time. References: http://secunia.com/advisories/14125/ http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0534 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0535 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0536 Solution: All MediaWiki users should upgrade to the latest available version: # emerge --sync # emerge --ask --oneshot --verbose ">=www-apps/mediawiki-1.3.11" Network Security Threat Level: Low Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

$3200.00
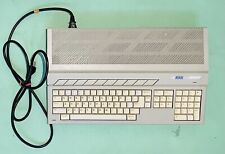
ATARI 4 Meg STACY ST (For Parts)
$500.00
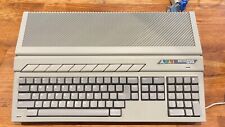
Vintage Atari 1040STf Computer with Mouse and Box, Minimal Testing, Pls Read
$149.99
Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
Atari 400/800/XL/XE Computer SIO2PC - PC/Mac Disk Drive Emulator Adapter/Device
$15.25
Rare Vintage Collectible Original Atari 800 Home Computer With Case - UNTESTED
$219.99
Atari 600 XL Vintage Home Computer Unused, CiB See Description For Details
$199.99
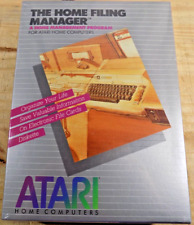
ATARI Home Computers HOME FILING MANAGER Software **SEALED NEW** 1982
$25.00
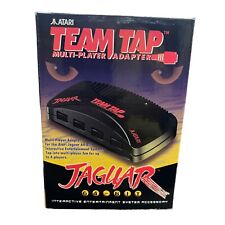
TEAM TAP Atari Jaguar Multi Player Adapter NEW In Box
$25.46
|
||
|
No Discussions have been posted on this vulnerability. |