|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200409-15] Webmin, Usermin: Multiple vulnerabilities in Usermin Vulnerability Assessment Details
|
[GLSA-200409-15] Webmin, Usermin: Multiple vulnerabilities in Usermin |
||
|
Webmin, Usermin: Multiple vulnerabilities in Usermin Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200409-15 (Webmin, Usermin: Multiple vulnerabilities in Usermin) There is an input validation bug in the webmail feature of Usermin. Additionally, the Webmin and Usermin installation scripts write to /tmp/.webmin without properly checking if it exists first. Impact The first vulnerability permits a remote attacker to inject arbitrary shell code in a specially-crafted e-mail. This could lead to remote code execution with the rights of the user running Webmin or Usermin. The second could permit local users who know Webmin or Usermin is going to be installed to have arbitrary files be overwritten by creating a symlink by the name /tmp/.webmin that points to some target file, e.g. /etc/passwd. Workaround There is no known workaround at this time. References: http://secunia.com/advisories/12488/ http://www.webmin.com/uchanges.html Solution: All Usermin users should upgrade to the latest version: # emerge sync # emerge -pv ">=app-admin/usermin-1.090" # emerge ">=app-admin/usermin-1.090" All Webmin users should upgrade to the latest version: # emerge sync # emerge -pv ">=app-admin/webmin-1.160" # emerge ">=app-admin/webmin-1.160" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

AMD EPYC 7282 CPU Processor 16 Cores 32 Threads 2.8GHZ up to 3.2GHZ 120W no lock
$76.00
Intel - Core i7-12700K Desktop Processor 12 (8P+4E) Cores up to 5.0 GHz Unloc...
$419.99
AMD Ryzen 9 5950X 16-core 32-thread Desktop Processor
$319.99
Intel - Core i9-12900K Desktop Processor 16 (8P+8E) Cores up to 5.2 GHz Unloc...
$619.99
Intel Core i7-6700 3.40 GHz QUAD Core (4 Core) Desktop Processor 8MB LGA 1151
$59.99
Intel Core i5-6500 3.2GHz 6MB SR2L6 / SR2BX Skt. FCLGA1151 Desktop Processor CPU
$24.50
Intel Core i7-14700K Unlocked Desktop Processor
$409.99
Intel Xeon Gold 6126 2.6 GHz LGA 3647 Server CPU Processor SR3B3
$17.99
Intel Core i7-13700KF Processor (5.4 GHz, 16 Cores, LGA 1700) Box
$350.00
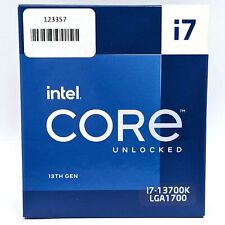
Intel Core i7-13700K 3.40GHz 16-Core CPU LGA1700 BX8071513700K
$339.99
|
||
|
No Discussions have been posted on this vulnerability. |