|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Fedora Local Security Checks >> Fedora Core 3 2005-188: HelixPlayer Vulnerability Assessment Details
|
Fedora Core 3 2005-188: HelixPlayer |
||
|
Check for the version of the HelixPlayer package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory FEDORA-2005-188 (HelixPlayer). The Helix Player 1.0 is an open-source media player built in the Helix Community for consumers. Built using GTK, it plays open source formats, like Ogg Vorbis and Theora using the powerful Helix DNA Client Media Engine. Update Information: Updated HelixPlayer packages that fixes two buffer overflow issues are now available. This update has been rated as having critical security impact by the Red Hat Security Response Team. A stack based buffer overflow bug was found in HelixPlayer's Synchronized Multimedia Integration Language (SMIL) file processor. An attacker could create a specially crafted SMIL file which would execute arbitrary code when opened by a user. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2005-0455 to this issue. A buffer overflow bug was found in the way HelixPlayer decodes WAV files. A possible hacker could create a specially crafted WAV file which could execute arbitrary code when opened by a user. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2005-0611 to this issue. All users of HelixPlayer are advised to upgrade to this updated package, which contains HelixPlayer 1.0.3 which is not vulnerable to these issues. Solution : Get the newest Fedora Updates Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

ASUS H110M-R Motherboard Intel 6th/7th Gen LGA1151 DDR4 Micro-ATX i/o shield
$42.00
***NEW*** BCM RX67Q Gaming Motherboard | Intel Q67 2nd/3rd Gen. | LGA1155 | DDR3
$29.77
Asus H110M-C Rev 1.03 mATX Desktop Motherboard LGA 1151/Socket H4 DDR4 SDRAM
$26.99
Asus H81M-C Intel LGA1150 DDR3 Desktop Motherboard MicroATX Socket H3
$24.99
MSI A320M-A PRO AM4 AMD A320 USB3.2 Gen1 Micro-ATX Motherboard
$46.99
Micro ATX Desktop Motherboard ASUS H110M-C LGA 1151
$31.95
ASUS Prime Q270M-C LGA1151 DP HDMI VGA SATA 6GB/s USB 3.0 MicroATX Motherboard
$37.99
Gigabyte AMD B550 UD AC Gaming Motherboard - AMD B550 Chipset - AM4 Socket - AMD
$89.99
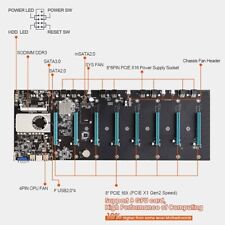
BTC-S37 Mining Motherboard Kit /w SSD & Ram Preinstalled
$59.99
ASRock B250M-HDV LGA 1151 Micro ATX DDR4 Desktop Motherboard w/ IO Shield
$54.99
|
||
|
No Discussions have been posted on this vulnerability. |