|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA921] DSA-921-1 kernel-source-2.4.27 Vulnerability Assessment Details
|
[DSA921] DSA-921-1 kernel-source-2.4.27 |
||
|
DSA-921-1 kernel-source-2.4.27 Detailed Explanation for this Vulnerability Assessment Several local and remote vulnerabilities have been discovered in the Linux kernel that may lead to a denial of service or the execution of arbitrary code. The Common Vulnerabilities and Exposures project identifies the following problems: Alexander Nyberg discovered that the ptrace() system call does not properly verify addresses on the amd64 architecture which can be exploited by a local attacker to crash the kernel. A problem in the offset handling in the xattr file system code for ext3 has been discovered that may permit users on 64-bit systems that have access to an ext3 filesystem with extended attributes to cause the kernel to crash. A vulnerability has been discovered in the ptrace() system call on the amd64 architecture that permits a local attacker to cause the kernel to crash. A vulnerability has been discovered in the stack segment fault handler that could permit a local attacker to cause a stack exception that will lead the kernel to crash under certain circumstances. Ilja van Sprundel discovered a race condition in the IA32 (x86) compatibility execve() systemcall for amd64 and IA64 that permits local attackers to cause the kernel to panic and possibly execute arbitrary code. Balazs Scheidler discovered that a local attacker could call setsockopt() with an invalid xfrm_user policy message which would cause the kernel to write beyond the boundaries of an array and crash. Vladimir Volovich discovered a bug in the zlib routines which are also present in the Linux kernel and permits remote attackers to crash the kernel. Another vulnerability has been discovered in the zlib routines which are also present in the Linux kernel and permits remote attackers to crash the kernel. A null pointer dereference in ptrace when tracing a 64-bit executable can cause the kernel to crash. Andreas Gruenbacher discovered a bug in the ext2 and ext3 file systems. When data areas are to be shared among two inodes not all information were compared for equality, which could expose wrong ACLs for files. Chad Walstrom discovered that the ipt_recent kernel module to stop SSH bruteforce attacks could cause the kernel to crash on 64-bit architectures. An error in the NAT code permits remote attackers to cause a denial of service (memory corruption) by causing two packets for the same protocol to be NATed at the same time, which leads to memory corruption. The following matrix explains which kernel version for which architecture fix the problems mentioned above: We recommend that you upgrade your kernel package immediately and reboot the machine. Solution : http://www.debian.org/security/2005/dsa-921 Network Security Threat Level: High Networks Security ID: 14477 Vulnerability Assessment Copyright: This script is (C) 2006 Michel Arboi |
||
|
Cables, Connectors |

Vintage 5362 IBM System/36 Mini-Computer Mainframe 5291 2, CRT Terminal DM12N501
$249.99
IBM Type 4869 External 5 1/4in Floppy Disk Drive Mainframe Collection - UNTESTED
$65.00
6 Vintage Computer Tape Reels mainframe 3200 5000 data ibm magnetic processor
$99.00
IBM Type 4869 External 5 1/4in Floppy Disk Drive Mainframe Collection
$145.99
Digital DEC LK201AA Terminal Keyboard RJ11 Connection Mainframe in original Box
$94.95
VINTAGE IBM Type 4869 External 5 1/4" ~ Floppy Disk Drive Mainframe ~
$159.99
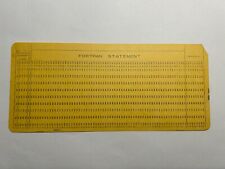
2 - VINTAGE MAINFRAME Fortran Format Punch Cards - IBM 80 columns
$3.49
Cray Research Supercomputer Cray X-MP ECL Logic Board
$149.99
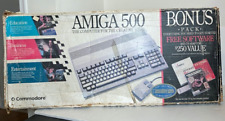
Commodore Amiga 500 Computer w/Mouse and Amiga A520 RF Modulator As Is Untested
$299.99
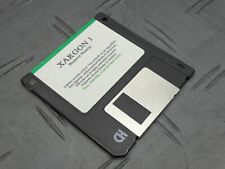
Xargon 1 Beyond Reality RARE Game Floppy 3.5” Floppy Mainframe Collection
$349.99
|
||
|
No Discussions have been posted on this vulnerability. |