|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA810] DSA-810-1 mozilla Vulnerability Assessment Details
|
[DSA810] DSA-810-1 mozilla |
||
|
DSA-810-1 mozilla Detailed Explanation for this Vulnerability Assessment Several problems have been discovered in Mozilla, the web browser of the Mozilla suite. Since the usual praxis of backporting apparently does not work for this package, this update is basically version 1.7.10 with the version number rolled back, and hence still named 1.7.8. The Common Vulnerabilities and Exposures project identifies the following problems: A vulnerability has been discovered in Mozilla that permits remote attackers to inject arbitrary Javascript from one page into the frameset of another site. The browser user interface does not properly distinguish between user-generated events and untrusted synthetic events, which makes it easier for remote attackers to perform dangerous actions that normally could only be performed manually by the user. XML scripts ran even when Javascript disabled. It is possible for a remote attacker to execute a callback function in the context of another domain (i.e. frame). Missing input sanitising of InstallVersion.compareTo() can cause the application to crash. Remote attackers could steal sensitive information such as cookies and passwords from web sites by accessing data in alien frames. It is possible for a Javascript dialog box to spoof a dialog box from a trusted site and facilitates phishing attacks. Remote attackers could modify certain tag properties of DOM nodes that could lead to the execution of arbitrary script or code. The Mozilla browser family does not properly clone base objects, which permits remote attackers to execute arbitrary code. For the stable distribution (sarge) these problems have been fixed in version 1.7.8-1sarge2. For the unstable distribution (sid) these problems have been fixed in version 1.7.10-1. We recommend that you upgrade your Mozilla packages. Solution : http://www.debian.org/security/2005/dsa-810 Network Security Threat Level: High Networks Security ID: 14242 Vulnerability Assessment Copyright: This script is (C) 2007 Michel Arboi |
||
|
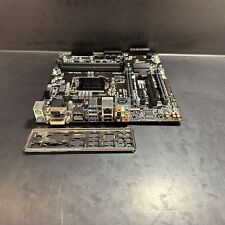
Cables, Connectors |

ASUS H110M-R Motherboard Intel 6th/7th Gen LGA1151 DDR4 Micro-ATX i/o shield
$42.00
***NEW*** BCM RX67Q mATX Gaming Motherboard Combo | Intel i5-3470 | 16GB DDR3
$49.77
Micro ATX Desktop Motherboard ASUS H110M-C LGA 1151
$31.95
ASUS Prime Z390-A LGA 1151 Intel Z390 SATA USB 3.1 ATX Motherboard NO I/O
$99.00
Gigabyte AMD B550 UD AC Gaming Motherboard - AMD B550 Chipset - AM4 Socket - AMD
$89.99
Gigabyte GA-Q170M-D3H-GSM LGA1151 DDR4 Desktop Motherboard + I/O Plate (READ)
$45.95
ASUS H110M-C LGA 1151 Micro ATX Motherboard 8GB RAM No CPU
$39.99
Asrock Z390 Phantom Gaming 4S/AC Wifi 8th/9th Gen Intel 1151 Motherboard Bulk
$47.35
ASUS PRIME Z690-P WIFI D4 ATX Motherboard Intel LGA1700 DDR4 HDMI
$99.99
GIGABYTE MB10-Datto Motherboard Xeon D-1521- SR2DF 2.40 GHz- Open Box
$121.50
|
||
|
No Discussions have been posted on this vulnerability. |