|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA764] DSA-764-1 cacti Vulnerability Assessment Details
|
[DSA764] DSA-764-1 cacti |
||
|
DSA-764-1 cacti Detailed Explanation for this Vulnerability Assessment Several vulnerabilities have been discovered in cacti, a round-robin database (RRD) tool that helps create graphs from database information. The Common Vulnerabilities and Exposures Project identifies the following problems: Maciej Piotr Falkiewicz and an anonymous researcher discovered an input validation bug that permits a possible hacker to include arbitrary PHP code from remote sites which will permit the execution of arbitrary code on the server running cacti. Due to missing input validation cacti permits a remote attacker to insert arbitrary SQL statements. Maciej Piotr Falkiewicz discovered an input validation bug that permits a possible hacker to include arbitrary PHP code from remote sites which will permit the execution of arbitrary code on the server running cacti. Stefan Esser discovered that the update for the above mentioned vulnerabilities does not perform proper input validation to protect against common attacks. Stefan Esser discovered that the update for CVE-2005-1525 permits remote attackers to modify session information to gain rights and disable the use of addslashes to protect against SQL injection. For the old stable distribution (woody) these problems have been fixed in version 0.6.7-2.5. For the stable distribution (sarge) these problems have been fixed in version 0.8.6c-7sarge2. For the unstable distribution (sid) these problems have been fixed in version 0.8.6f-2. We recommend that you upgrade your cacti package. Solution : http://www.debian.org/security/2005/dsa-764 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is (C) 2007 Michel Arboi |
||
|
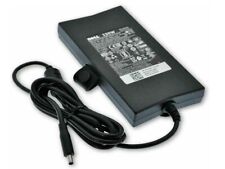
Cables, Connectors |

OEM 130W Charger For Dell XPS 15 9530 9550 9560 9570 7590 06TTY6 Power Adapter
$35.99
M1MYR Dell OEM 130W AC Adapter 4.5mm Small Tip 4 Precision 5520 5530 M20 4MFJT
$18.04
NEW OEM Dell Inspiron 14 5406 P126G Laptop Battery 11.25V 40Wh JK6Y6 CF5RH
$37.00
OEM Dell Inspiron 11 13 14 15 17 3000 5000 7000 AC Adapter Charger 65W 4.5mm Tip
$10.99
Genuine OEM Dell 90W Laptop Charger AC Adapter 19.5V 4.62A 50-60 Hz white tip
$8.74
OEM 130W USB-C Type-C Charger for Dell XPS 15 9500 9570 9575 17 9700 DA130PM170
$35.88
Genuine OEM 65W Dell PA-12 AC Adapter Charger 928G4 06TM1C LA65NS2-01 7.4*5.0mm
$14.99
Dell OEM Latitude 12 Rugged 7214 / 7204 Touchscreen LCD Complete Assembly
$39.00
Genuine OEM 42wh YRDD6 Battery For Dell Inspiron 3493 3582 3583 3584 7586 3793
$32.89
|
||
|
No Discussions have been posted on this vulnerability. |