|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA394] DSA-394-1 openssl095 Vulnerability Assessment Details
|
[DSA394] DSA-394-1 openssl095 |
||
|
DSA-394-1 openssl095 Detailed Explanation for this Vulnerability Assessment Steve Henson of the OpenSSL core team identified and prepared fixes for a number of vulnerabilities in the OpenSSL ASN1 code that were discovered after running a test suite by British National Infrastructure Security Coordination Centre (NISCC). A bug in OpenSSLs SSL/TLS protocol was also identified which causes OpenSSL to parse a client certificate from an SSL/TLS client when it should reject it as a protocol error. The Common Vulnerabilities and Exposures project identifies the following problems: Integer overflow in OpenSSL that permits remote attackers to cause a denial of service (crash) via an SSL client certificate with certain ASN.1 tag values. OpenSSL does not properly track the number of characters in certain ASN.1 inputs, which permits remote attackers to cause a denial of service (crash) via an SSL client certificate that causes OpenSSL to read past the end of a buffer when the long form is used. Double-free vulnerability permits remote attackers to cause a denial of service (crash) and possibly execute arbitrary code via an SSL client certificate with a certain invalid ASN.1 encoding. This bug was only present in OpenSSL 0.9.7 and is listed here only for reference. For the stable distribution (woody) this problem has been fixed in openssl095 version 0.9.5a-6.woody.3. This package is not present in the unstable (sid) or testing (sarge) distribution. We recommend that you upgrade your libssl095a packages and restart services using this library. Debian doesn't ship any packages that are linked against this library. The following commandline (courtesy of Ray Dassen) produces a list of names of running processes that have libssl095 mapped into their memory space: find /proc -name maps -exec egrep -l 'libssl095' {} /dev/null \ | sed -e 's/[^0-9]//g' | xargs --no-run-if-empty ps --no-headers -p | sed -e 's/^\+//' -e 's/ \+/ /g' | cut -d ' ' -f 5 | sort | uniq You should restart the associated services. Solution : http://www.debian.org/security/2003/dsa-394 Network Security Threat Level: High Networks Security ID: 8732 Vulnerability Assessment Copyright: This script is (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Vintage 1960s Donner Model 3000 Analog Computer ~ MUSEUM PIECE Extremely Rare
$4000.00
NEC Multisync II JC-1402HMA VGA EGA CGA Analog TTL Computer Monitor Vintage 1988
$699.99
NEW Aquarius+ Computer Signature Edition - 8Bit Retro System
$239.00
Apple Macintosh SE/30 M5119 Computer 8MB RAM Recapped Working *See Description*
$450.00
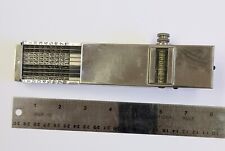
Landen Computer. Circa 1898. the Rapid Computer Company. With Original Case.
$425.00
IBM Modem Saver Phone Line Tester
$7.99
Burr Brown Analog Computer parts Circuit boards w Helipot Potentiometers 1631a
$85.00
Vintage Apple Macintosh Plus Completely Recapped #M0001A 1MB
$649.95
Extron RGB-160XI Analog Computer Video 60-378-01
$187.06
Wooting Two HE Mechanical Keyboard Analog Linear Lekker Switches
$299.99
|
||
|
No Discussions have been posted on this vulnerability. |