|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA254] DSA-254-1 traceroute-nanog Vulnerability Assessment Details
|
[DSA254] DSA-254-1 traceroute-nanog |
||
|
DSA-254-1 traceroute-nanog Detailed Explanation for this Vulnerability Assessment A vulnerability has been discovered in NANOG traceroute, an enhanced version of the Van Jacobson/BSD traceroute program. A buffer overflow occurs in the 'get_origin()' function. Due to insufficient bounds checking performed by the whois parser, it may be possible to corrupt memory on the system stack. This vulnerability can be exploited by a remote attacker to gain root rights on a target host. Though, most probably not in Debian. The Common Vulnerabilities and Exposures (CVE) project additionally identified the following vulnerabilities which were already fixed in the Debian version in stable (woody) and oldstable (potato) and are mentioned here for completeness (and since other distributions had to release a separate advisory for them): Fortunately, the Debian package drops rights quite early after startup, so those problems are not likely to result in an exploit on a Debian machine. For the current stable distribution (woody) the above problem has been fixed in version 6.1.1-1.2. For the old stable distribution (potato) the above problem has been fixed in version 6.0-2.2. For the unstable distribution (sid) these problems have been fixed in version 6.3.0-1. We recommend that you upgrade your traceroute-nanog package. Solution : http://www.debian.org/security/2003/dsa-254 Network Security Threat Level: High Networks Security ID: 4956, 6166, 6274, 6275 Vulnerability Assessment Copyright: This script is (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Intel Pentium A80502-166 Vintage CPU | UNTESTED - READ DESCRIPTION
$19.55
(5) Vintage DiskBank floppy Disk Storage Holders Vintage
$29.95
Vintage Logitech ScanMan Hand Held Scanner B5N-1706 Made in Japan
$14.99
Rare Vintage Burroughs Computer Data Processing Tape Approx 2500 Ft
$59.99
Vintage CARDCO Vic-20 C64 +4 C16 and C128 Parallel Printer Interface Card - QTY
$19.99
Vintage Fellows 5.25" Multi Media Storage Floppy Disk Tray 90111
$13.99
Vintage Atari STM1 Rollerball Two-Button Mouse Serial X5045136618
$69.99
Vintage IBM Thinkpad T43 14" LCD Laptop 55GB HDD Pentium M 1.73GHz 1GB RAM WinXP
$199.99
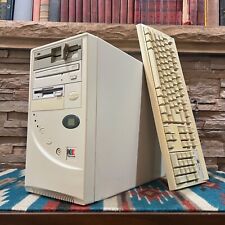
Vintage Retro AT PC Tower - Pentium MMX 166 24MB 3.5 5.25" Sound Keyboard POSTS
$199.00
Vintage 1986 IBM 1389262 Model M buckling spring terminal keyboard -1 keycap
$150.00
|
||
|
No Discussions have been posted on this vulnerability. |