|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA1227] DSA-1227-1 mozilla-thunderbird Vulnerability Assessment Details
|
[DSA1227] DSA-1227-1 mozilla-thunderbird |
||
|
DSA-1227-1 mozilla-thunderbird Detailed Explanation for this Vulnerability Assessment Several security related problems have been discovered in Mozilla and derived products such as Mozilla Thunderbird. The Common Vulnerabilities and Exposures project identifies the following vulnerabilities: Tomas Kempinsky discovered that malformed FTP server responses could lead to denial of service. Ulrich Kühn discovered that the correction for a cryptographic flaw in the handling of PKCS-1 certificates was incomplete, which permits the forgery of certificates. "shutdown" discovered that modification of JavaScript objects during execution could lead to the execution of arbitrary JavaScript bytecode. Jesse Ruderman and Martijn Wargers discovered several crashes in the layout engine, which might also permit execution of arbitrary code. Igor Bukanov and Jesse Ruderman discovered several crashes in the JavaScript engine, which might permit execution of arbitrary code. This update also addresses several crashes, which could be triggered by malicious websites and fixes a regression introduced in the previous Mozilla update. For the stable distribution (sarge) these problems have been fixed in version 1.0.4-2sarge13. For the unstable distribution (sid) these problems have been fixed in the current icedove package 1.5.0.8. We recommend that you upgrade your mozilla-thunderbird package. Solution : http://www.debian.org/security/2006/dsa-1227 Network Security Threat Level: High Networks Security ID: 19678, 20957 Vulnerability Assessment Copyright: This script is (C) 2006 Michel Arboi |
||
|
Cables, Connectors |

Commodore Amiga A2386SX Bridge board
$900.00
Brand New Amiga 4000T Keyboard
$299.99
Mini External OLED AMIGA Gotek Floppy Drive Emulator For Amiga 500/500+/600/1200
$39.20
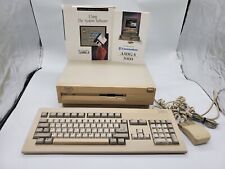
Commodore Amiga 3000 030 25Mhz + Keyboard + Mouse - Amiga OS 3.2 - WORKS 100%
$1599.99
Commodore Amiga Stereo Sound Sampler Techno Sound Turbo Technosound HW & SW pack
$50.99
Amiga 500 Gotek Custom Mount USB Floppy Emulator - Complete Kit with Gotek
$65.00
Apollo Vampire 600v2 / 600 V2 FPGA Accelerator Card for Commodore Amiga 600
$350.00
Commodore Amiga 1060 Side Car Expansion "IBM PC EMULATOR" VERY RARE COLLECTIBLE
$1499.95
AMIGA 500 COMPUTER COMMODORE Complete in Box Powers/untested Good Condition
$370.00
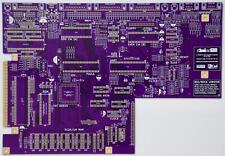
Raemixx500 Commodore Amiga500+ V2 Remake PCB Gold Plated
$35.15
|
||
|
No Discussions have been posted on this vulnerability. |