|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> Talentsoft Web+ reveals install path Vulnerability Assessment Details
|
Talentsoft Web+ reveals install path |
||
|
Checks for Webplus install path disclosure Detailed Explanation for this Vulnerability Assessment Summary : The remote web server is affected by an information disclosure flaw. Description : The remote host appears to be running Web+ Application Server. The version of Web+ installed on the remote host reveals the physical path of the application when it receives a script file error. See also : http://www.talentsoft.com/Issues/IssueDetail.wml?ID=WP197 Solution : Apply the vendor-supplied patch. Network Security Threat Level: Low / CVSS Base Score : 2 (AV:R/AC:L/Au:NR/C:P/A:N/I:N/B:N) Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 David Kyger |
||
|
Cables, Connectors |

Cisco ASA 5520 Adaptive Security Appliance
$56.75
NetFu Firewall 1U, Intel CPU, 8 x Gigabit, SFP, w/ pfSense, Others, NEW OPTIONS
$541.85
Fortinet FortiGate-40C Network Security Firewall
$42.50
Fortinet Fortigate FG-61E | Firewall Network Security Appliance
$49.99
Fortinet FortiGate FG-40F Network Security Firewall
$100.00
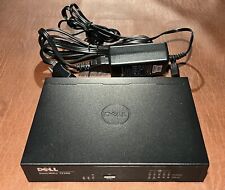
Dell SonicWall TZ300 5-Port Network Security Firewall Appliance APL28-0B4
$24.95
Fortinet Fortigate 70D Firewall Adapter Network Security Appliance
$52.00
OPNsense six-port Gigabit router/firewall on Lanner FW-7535 hardware
$69.00
Fortinet Fortiwifi 60D FG-60D Security Appliance Firewall / VPN w/ AC Adapter
$999.97
Fortinet FortiGate 60E & FortiAP 221E+ Network Security Firewall
$260.00
|
||
|
No Discussions have been posted on this vulnerability. |