|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200405-16] Multiple XSS Vulnerabilities in SquirrelMail Vulnerability Assessment Details
|
[GLSA-200405-16] Multiple XSS Vulnerabilities in SquirrelMail |
||
|
Multiple XSS Vulnerabilities in SquirrelMail Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200405-16 (Multiple XSS Vulnerabilities in SquirrelMail) Several unspecified cross-site scripting (XSS) vulnerabilities and a well hidden SQL injection vulnerability were found. An XSS attack permits an attacker to insert malicious code into a web-based application. SquirrelMail does not check for code when parsing variables received via the URL query string. Impact One of the XSS vulnerabilities could be exploited by a possible hacker to steal cookie-based authentication credentials from the user's browser. The SQL injection issue could potentially be used by a possible hacker to run arbitrary SQL commands inside the SquirrelMail database with rights of the SquirrelMail database user. Workaround There is no known workaround at this time. All users are advised to upgrade to version 1.4.3_rc1 or higher of SquirrelMail. References: http://sourceforge.net/mailarchive/forum.php?thread_id=4199060&forum_id=1988 http://www.securityfocus.com/bid/10246/ http://www.cert.org/advisories/CA-2000-02.html Solution: All SquirrelMail users should upgrade to the latest stable version: # emerge sync # emerge -pv ">=net-mail/squirrelmail-1.4.3_rc1" # emerge ">=net-mail/squirrelmail-1.4.3_rc1" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Samsung Galaxy Tab A8 10.5" SM-X200 128GB Wifi Only Tablet Open Box
$149.99
Genuine Samsung Book Cover Keyboard for 14.6" Galaxy Tab S8 Ultra | S8 Ultra 5G
$89.99
Samsung - S Pen Creator Edition - White
$40.00
Samsung Galaxy Tab A9 (X110) 64GB 4GB RAM International Version (New)
$129.99
Samsung Galaxy 12.4 Inch Slim Keyboard For S7+ | S7 FE | S8+ | S8+ 5G EF-DT730
$49.99
SAMSUNG AM-P613NZBMXAR Galaxy S6 Lite 2022 10.4" 64GB Wi-Fi Tablet With S Pen,
$134.00
Samsung Galaxy Tab E 8" 16GB Black SM-T377V (Verizon) Android Tablet IG1000
$30.35
Samsung Galaxy Chromebook Go, 14-inch, 32GB, Unlocked All Carriers - Silver
$109.99
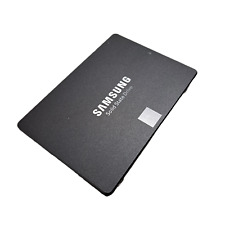
Samsung 870 EVO 500GB 2.5" SSD MZ-77E500
$30.00
Samsung 850 EVO 500GB 2.5" SSD MZ-75E500
$30.00
|
||
|
No Discussions have been posted on this vulnerability. |